How hackers use idle scans in port scan attacks
Por um escritor misterioso
Last updated 11 março 2025
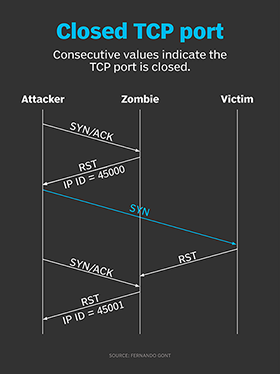
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
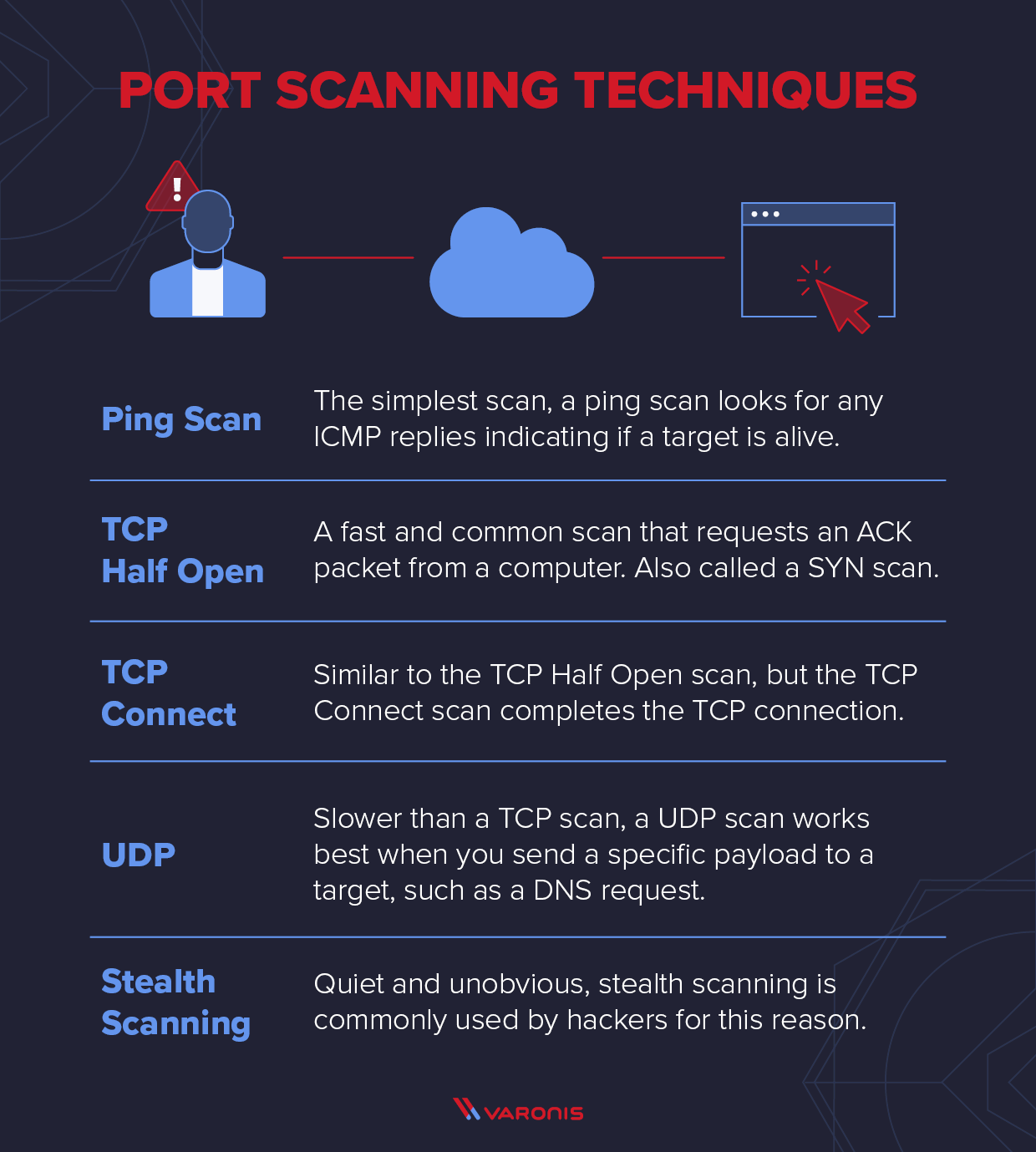
What is a Port Scanner and How Does it Work?
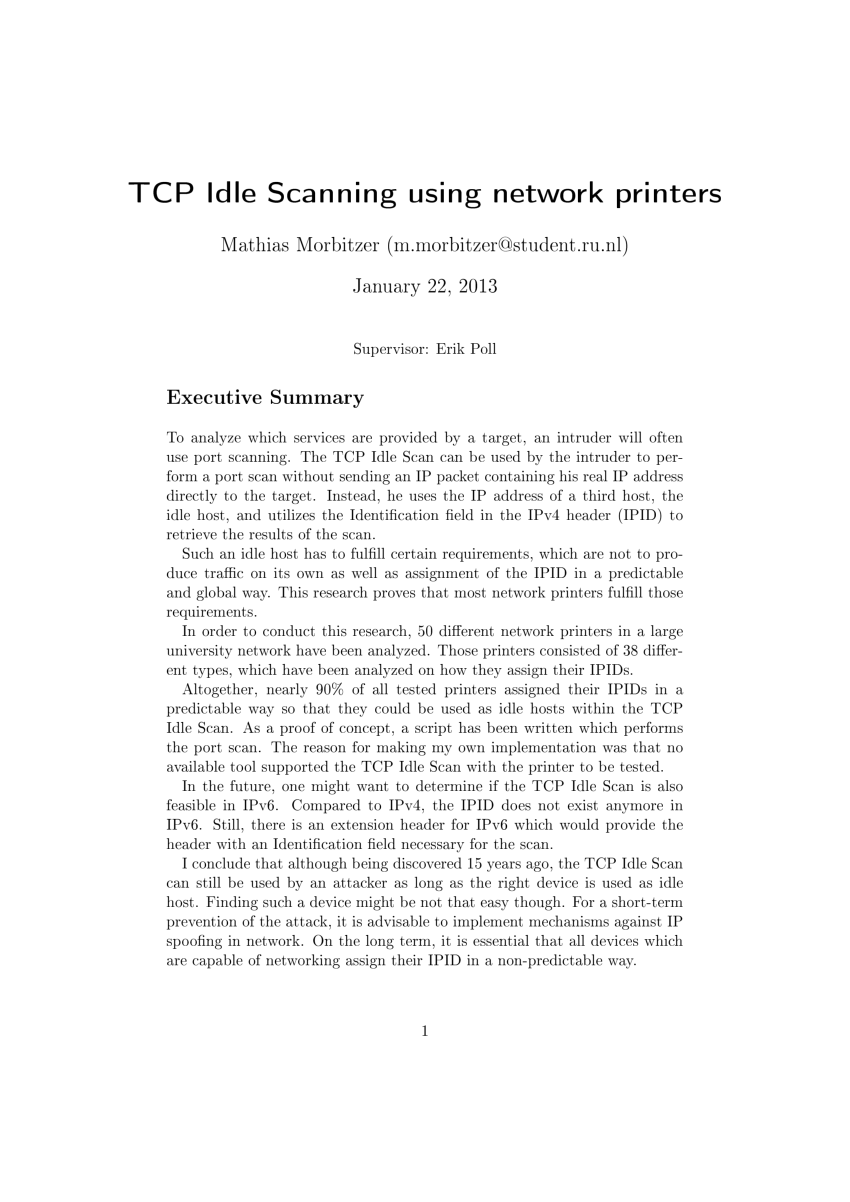
PDF) TCP Idle Scanning using network printers

NMAP by Shrikant Antre & Shobhit Gautam

How to Do an Idle Scan with Nmap « Null Byte :: WonderHowTo

Port Scanning - an overview
Essential Nmap Commands for System Admins - Penetration Testing Tools, ML and Linux Tutorials

Ethical Hacking: Scanning Networks (2016) Online Class
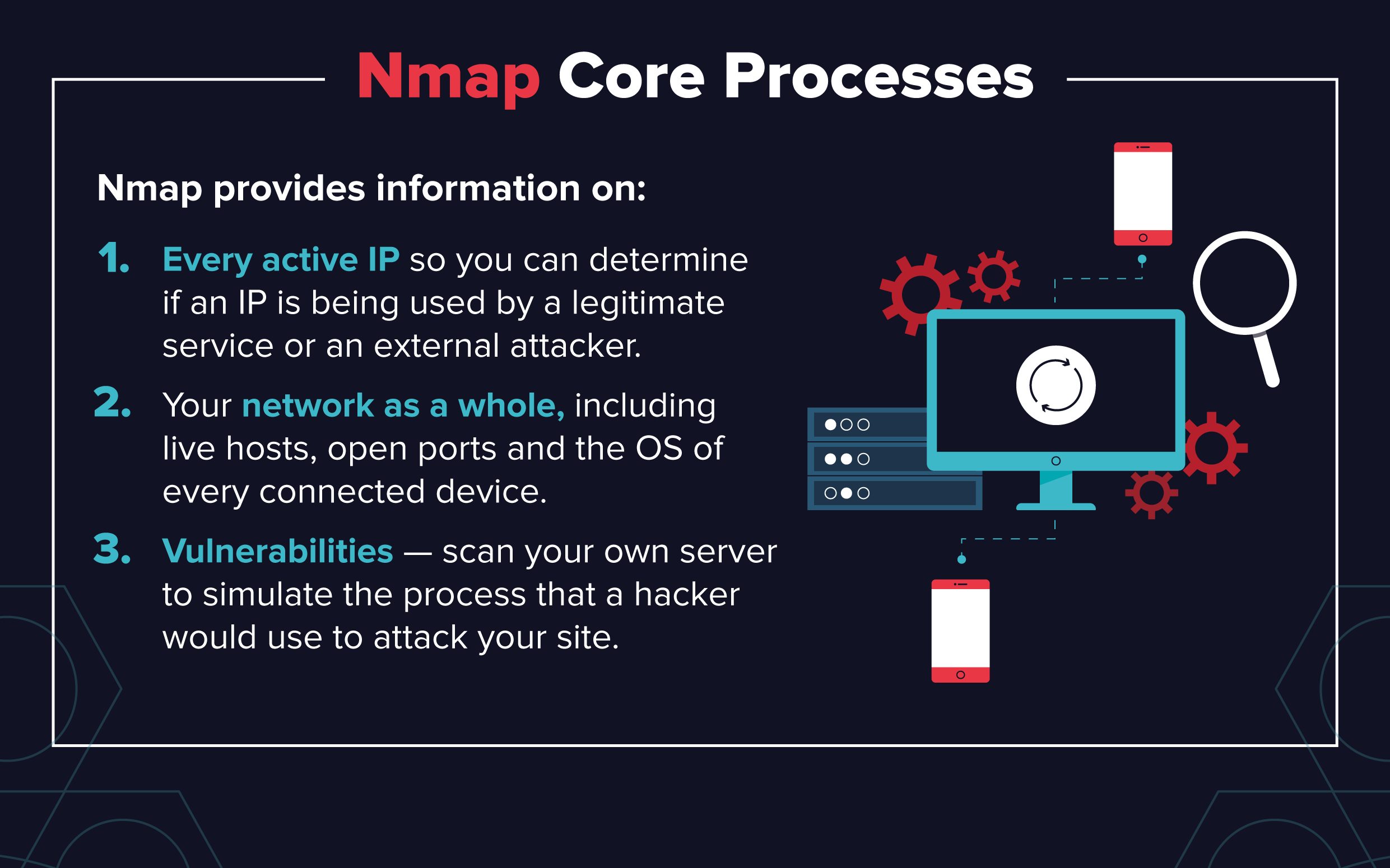
What Is Nmap? A Comprehensive Tutorial For Network Mapping
Nmap Advanced Port Scans, TryHackMe (THM), by Aircon

How hackers use idle scans in port scan attacks

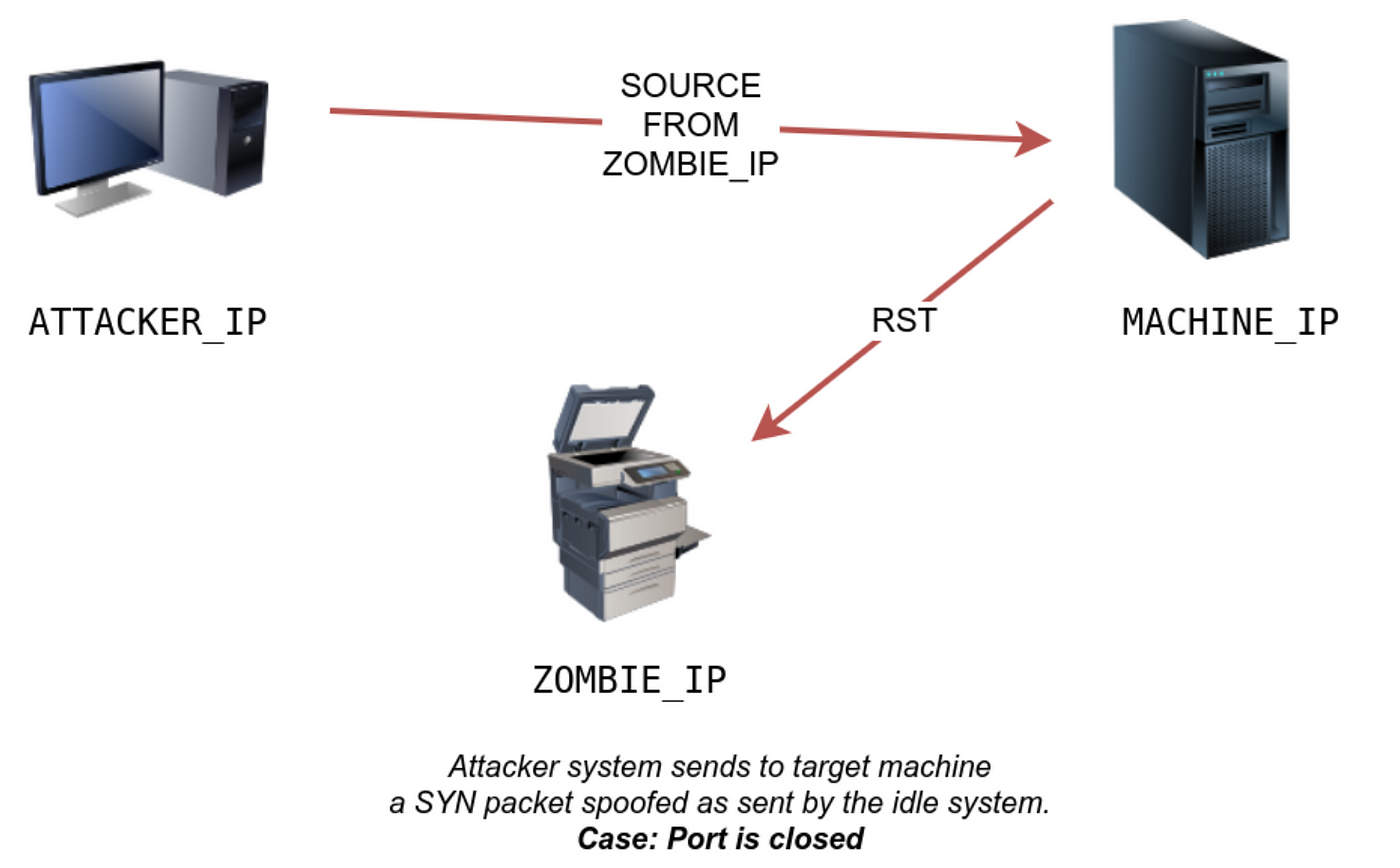
What is Idle Scan? ICterra Information and Communication Technologies
Recomendado para você
-
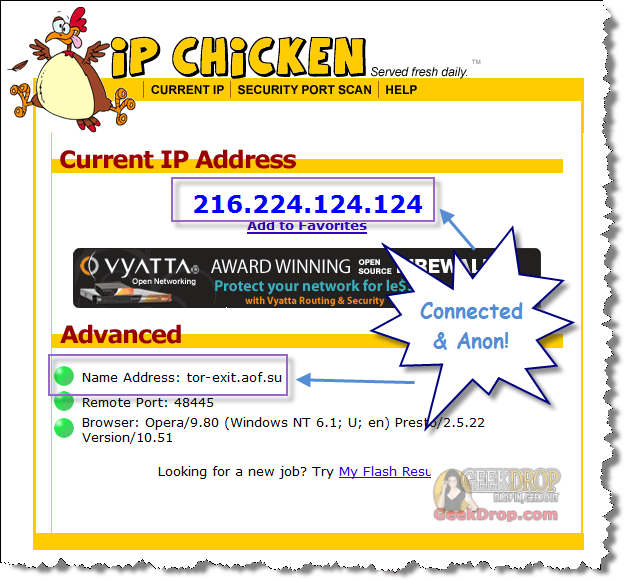
 IPChicken, Woo hoo! Lightspeed!, Richard De Guzman11 março 2025
IPChicken, Woo hoo! Lightspeed!, Richard De Guzman11 março 2025 -
:max_bytes(150000):strip_icc()/curl-command-ip-address-0bbe45c7243d42acaff9ddf2f117a7cb.png) How to Find Your IP Address on Windows 1011 março 2025
How to Find Your IP Address on Windows 1011 março 2025 -
Crossfire Philippines - [Notice] Data Transmission Error - Info Gathering Hello Mercenaries! We would like to ask some assistance to further address the issue regarding the Data Transmission Error. This will greatly11 março 2025
-
 Anonymous Security Scanning and Browsing11 março 2025
Anonymous Security Scanning and Browsing11 março 2025 -
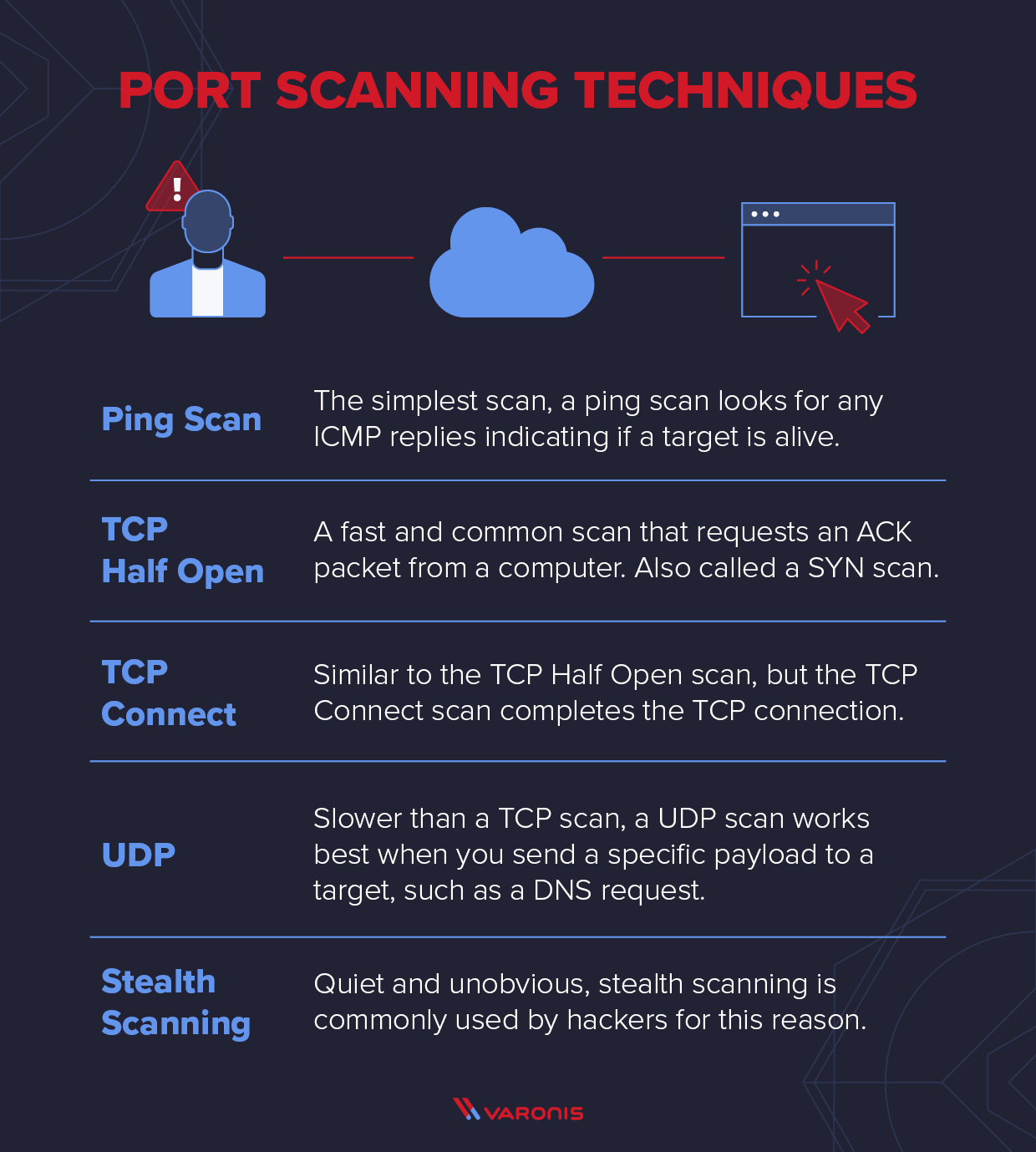 Explaining Port Scanning. A port scan is a common technique…, by Arth Awasthi11 março 2025
Explaining Port Scanning. A port scan is a common technique…, by Arth Awasthi11 março 2025 -
 How to Prevent Port Scan Attacks? - GeeksforGeeks11 março 2025
How to Prevent Port Scan Attacks? - GeeksforGeeks11 março 2025 -
 How To Use Tor With Opera Web Browser (With Polipo) For Beginners11 março 2025
How To Use Tor With Opera Web Browser (With Polipo) For Beginners11 março 2025 -
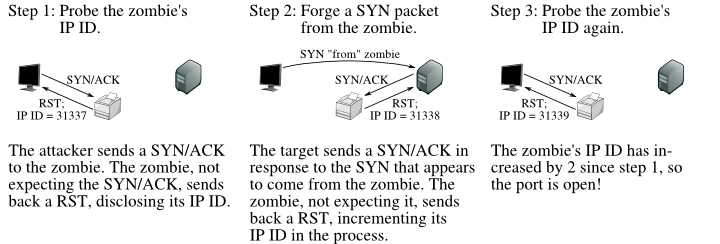 TCP Idle Scan (-sI) Nmap Network Scanning11 março 2025
TCP Idle Scan (-sI) Nmap Network Scanning11 março 2025 -
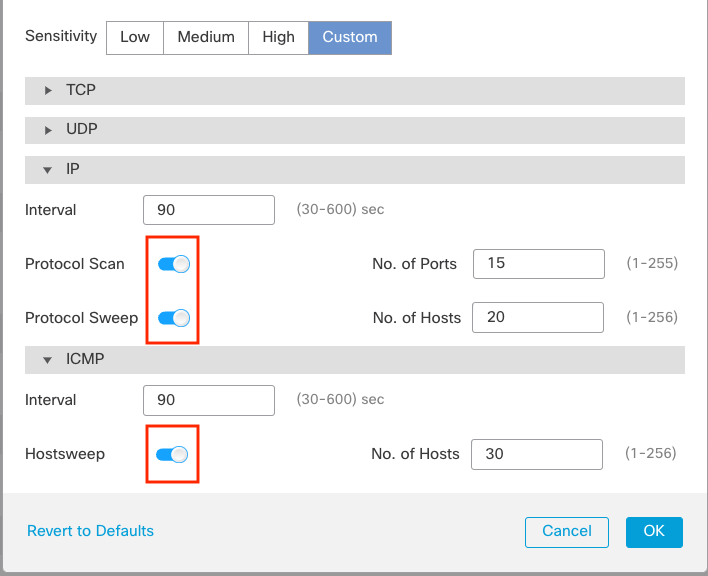 Port Scan Detection11 março 2025
Port Scan Detection11 março 2025 -
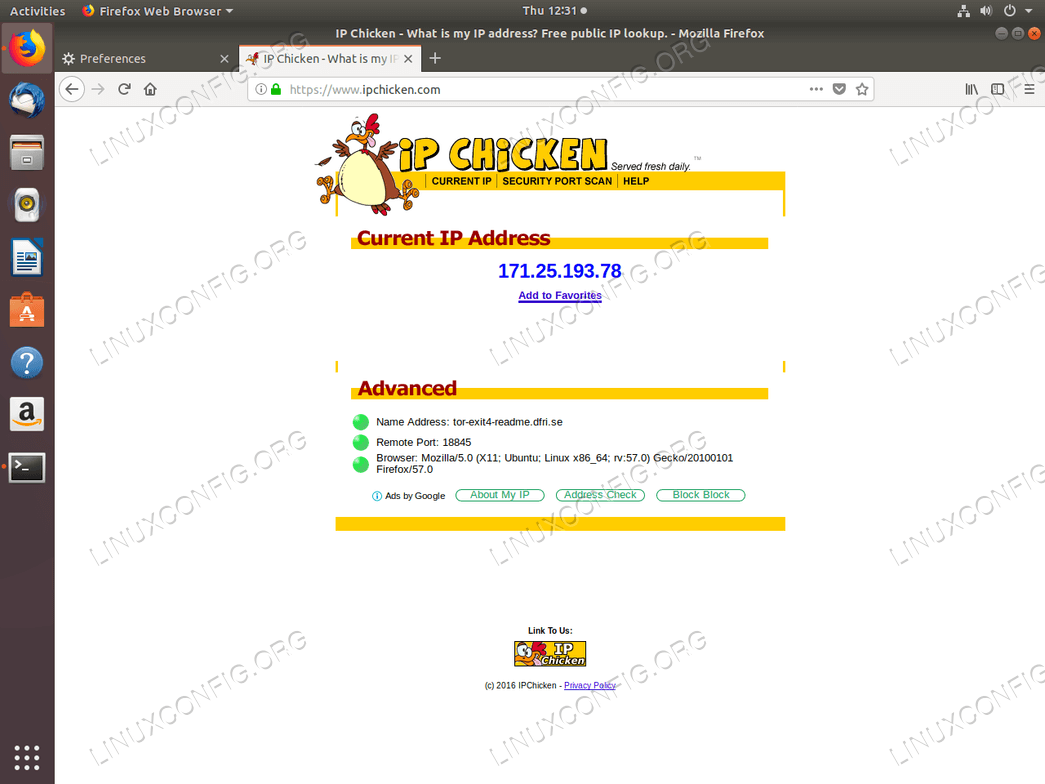 Install Tor on Ubuntu 18.04 Bionic Beaver Linux - Linux Tutorials - Learn Linux Configuration11 março 2025
Install Tor on Ubuntu 18.04 Bionic Beaver Linux - Linux Tutorials - Learn Linux Configuration11 março 2025
você pode gostar
-
 Rust - Day One Edition (Xbox One) – igabiba11 março 2025
Rust - Day One Edition (Xbox One) – igabiba11 março 2025 -
 Aspecto geral do jogo did?tico desenvolvido durante a pesquisa. A11 março 2025
Aspecto geral do jogo did?tico desenvolvido durante a pesquisa. A11 março 2025 -
 Alolan Raichu Pokemon Trade Go11 março 2025
Alolan Raichu Pokemon Trade Go11 março 2025 -
 Download FIFA 22 free for PC - CCM11 março 2025
Download FIFA 22 free for PC - CCM11 março 2025 -
 Summer Time Rendering Episode 21 Preview Hints at Shinpei's Longest Day11 março 2025
Summer Time Rendering Episode 21 Preview Hints at Shinpei's Longest Day11 março 2025 -
 FIGURA SURPRESA SERIE 11 ROBLOX SUNNY 038708 - FIGURA SURPRESA SERIE 11 ROBLOX SUNNY - SUNNY11 março 2025
FIGURA SURPRESA SERIE 11 ROBLOX SUNNY 038708 - FIGURA SURPRESA SERIE 11 ROBLOX SUNNY - SUNNY11 março 2025 -
Anime adventures new update and code #animeadventures #animeadventure11 março 2025
-
 Relógio De Parede Desenho Dragon Ball Vegeta Anime11 março 2025
Relógio De Parede Desenho Dragon Ball Vegeta Anime11 março 2025 -
a work in progress #poetry#comfort#nostalgia#mentalhealth11 março 2025
-
 Classroom of the Elite Season 2 Episode 1 Release Date and Time, COUNTDOWN11 março 2025
Classroom of the Elite Season 2 Episode 1 Release Date and Time, COUNTDOWN11 março 2025
![Crossfire Philippines - [Notice] Data Transmission Error - Info Gathering Hello Mercenaries! We would like to ask some assistance to further address the issue regarding the Data Transmission Error. This will greatly](https://lookaside.fbsbx.com/lookaside/crawler/media/?media_id=2958303717738978)
