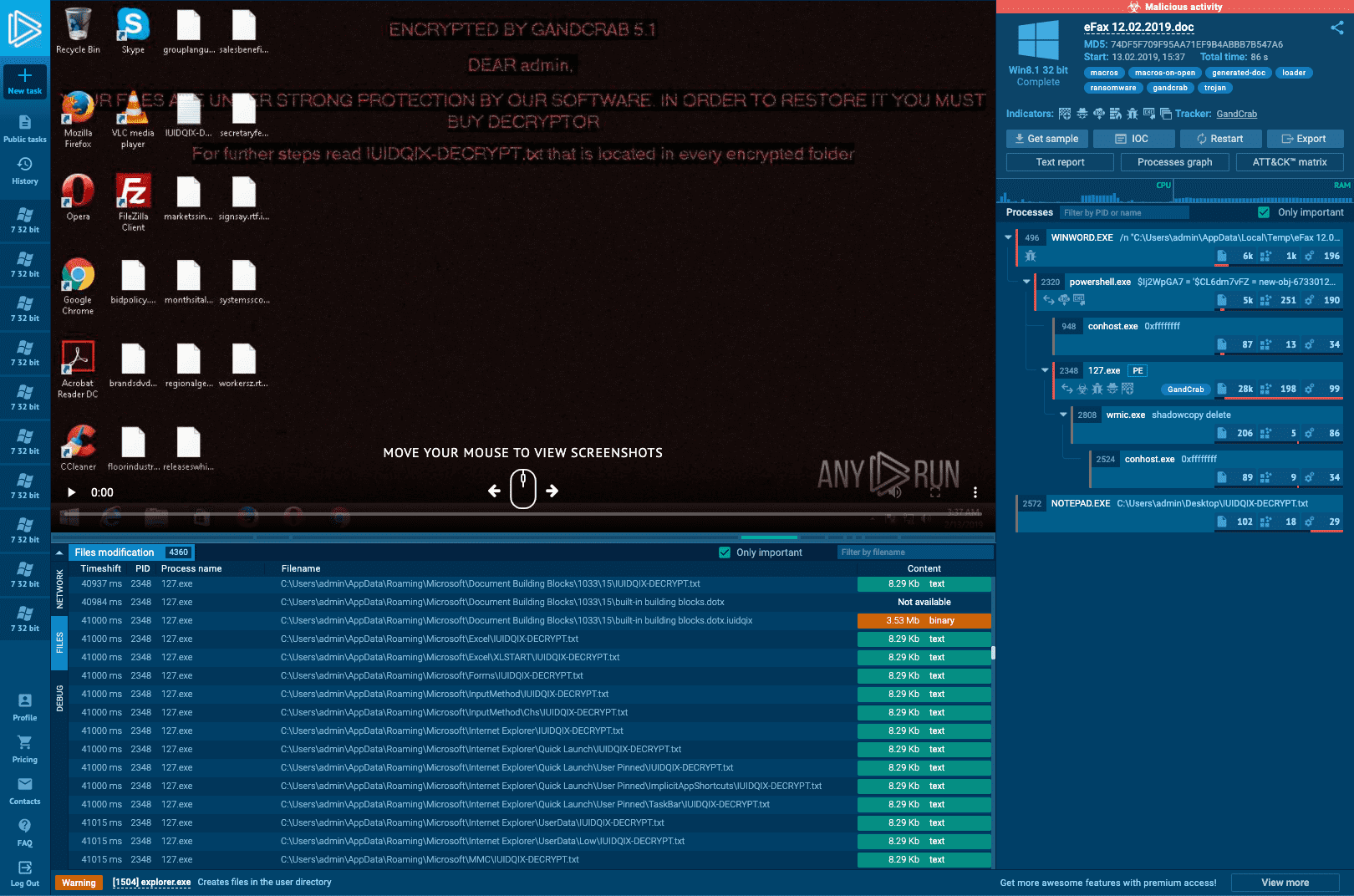
Malware analysis Malicious activity
Por um escritor misterioso
Last updated 29 março 2025

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks

Malware Analysis: Steps & Examples - CrowdStrike
Interactive Online Malware Sandbox
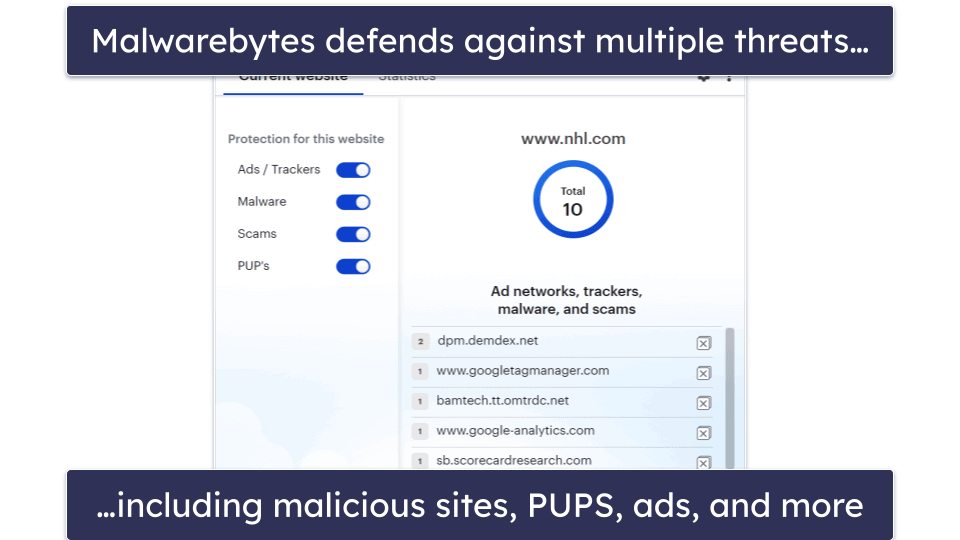
10 Best (REALLY FREE) Antivirus Software for Windows in 2023

Malware Analysis: Steps & Examples - CrowdStrike

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Malware analysis mykey_.rar Malicious activity

Malware analysis index.html Malicious activity
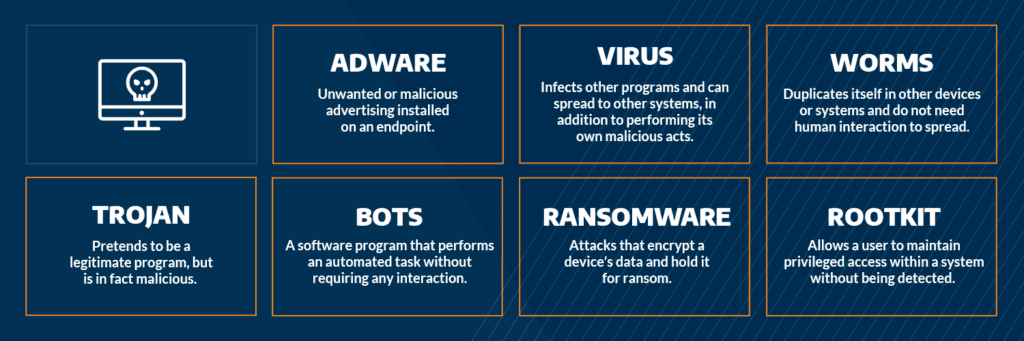
Most Common Malware Attacks

Malware Analysis: Protecting Your Network from Cyber Attacks

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
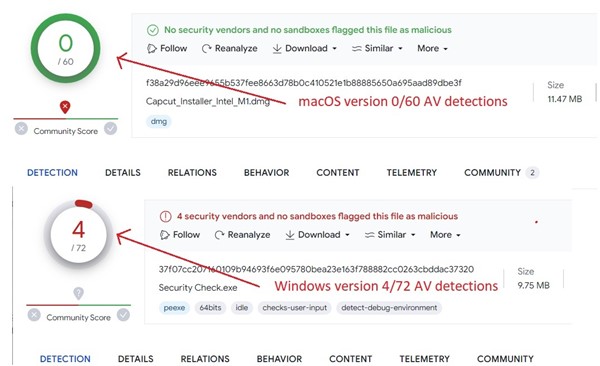
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows

AV-TEST Confirms Skyhigh Security Service Edge Delivers Superior Threat Protection in All Test Categories

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware Analysis Benefits Incident Response
Recomendado para você
-
 Home Tools29 março 2025
Home Tools29 março 2025 -
 Exploits :: PalXploits29 março 2025
Exploits :: PalXploits29 março 2025 -
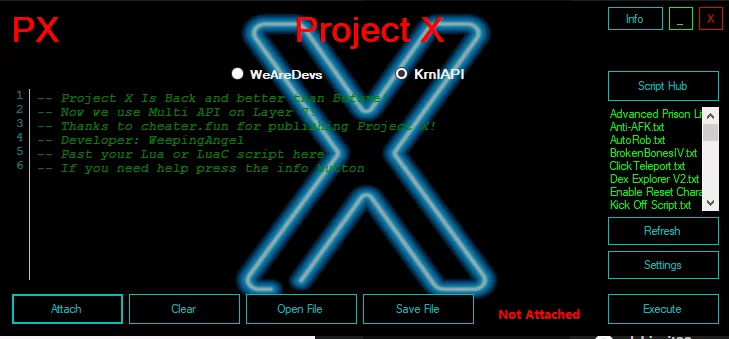 Project X Executor Roblox Beta – Caked By Petite29 março 2025
Project X Executor Roblox Beta – Caked By Petite29 março 2025 -
 JJSploit29 março 2025
JJSploit29 março 2025 -
 Error code 403 with VS when trying to inject wearedevs api, for29 março 2025
Error code 403 with VS when trying to inject wearedevs api, for29 março 2025 -
 Luau Goes Open Source! - Announcements - Developer Forum29 março 2025
Luau Goes Open Source! - Announcements - Developer Forum29 março 2025 -
 Malware analysis Malicious activity29 março 2025
Malware analysis Malicious activity29 março 2025 -
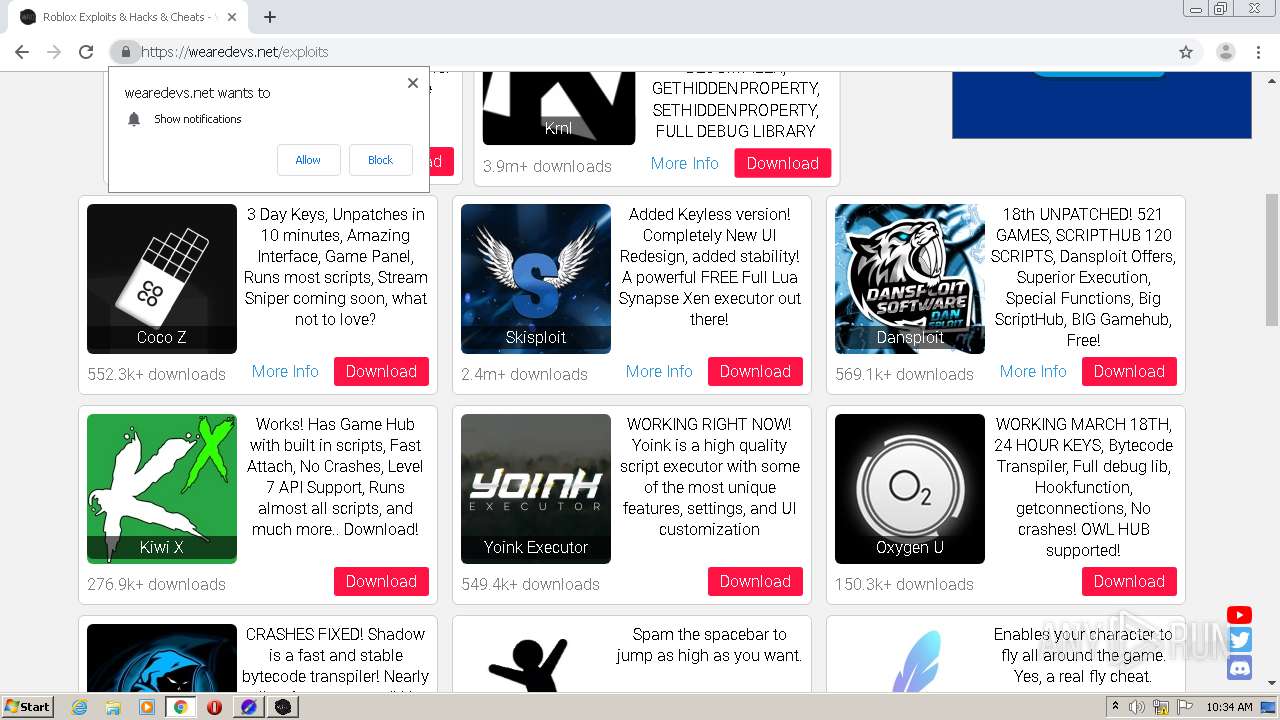
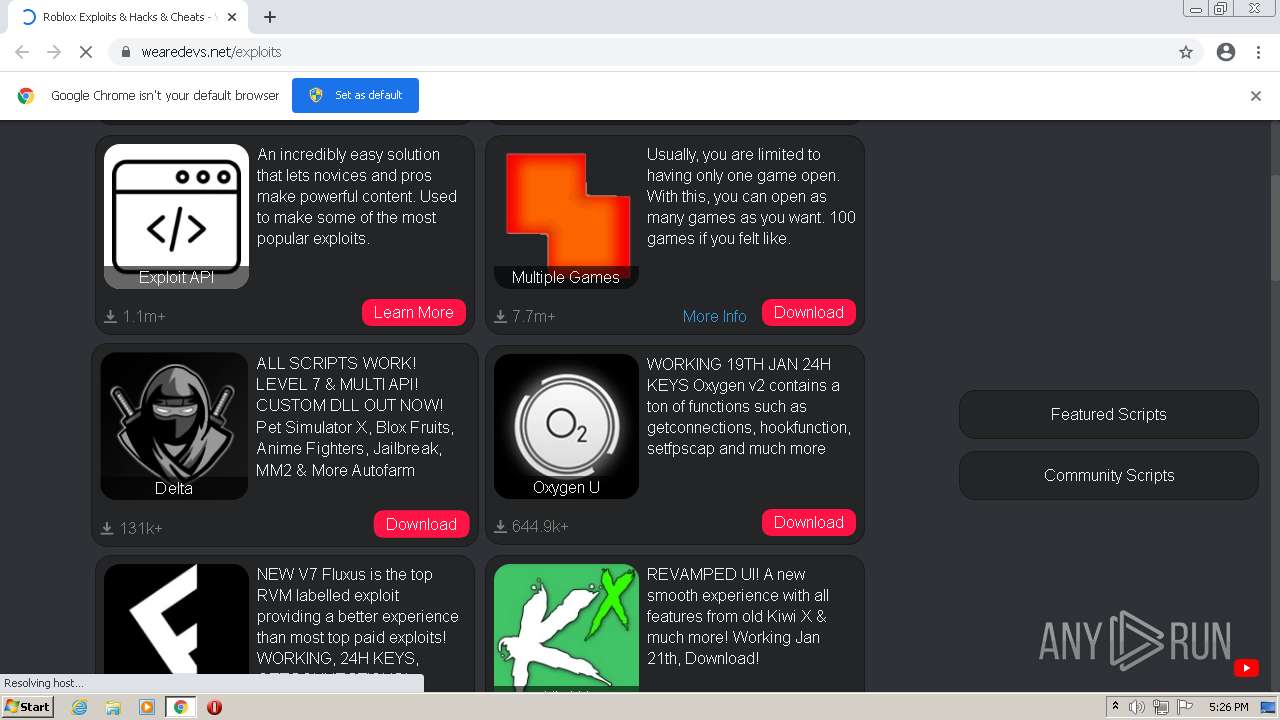
 Roblox Exploits & Hacks & Cheats - WeAreDevs29 março 2025
Roblox Exploits & Hacks & Cheats - WeAreDevs29 março 2025 -
![EXPOSE?] _TheRobloxian_ uses WRD API and says his exploit is](https://i.imgur.com/gZemmC0.png) EXPOSE?] _TheRobloxian_ uses WRD API and says his exploit is29 março 2025
EXPOSE?] _TheRobloxian_ uses WRD API and says his exploit is29 março 2025 -
FinlinSploit Premium V1.0 FREE by Finlin Cheats - Free download on29 março 2025
você pode gostar
-
 The Best Tennis Academies in The World – Functional Tennis29 março 2025
The Best Tennis Academies in The World – Functional Tennis29 março 2025 -
 Shinra Kusakabe Fire Force Anime 4K HD Mobile Smartphone and PC29 março 2025
Shinra Kusakabe Fire Force Anime 4K HD Mobile Smartphone and PC29 março 2025 -
 How to Watch Pokémon Master Journeys: The Series Part 3 on Netflix29 março 2025
How to Watch Pokémon Master Journeys: The Series Part 3 on Netflix29 março 2025 -
 Brinquedo Musical Teclado Infantil Hot Wheels Radical Fun29 março 2025
Brinquedo Musical Teclado Infantil Hot Wheels Radical Fun29 março 2025 -
 Camiseta Infantil Luccas Neto29 março 2025
Camiseta Infantil Luccas Neto29 março 2025 -
 Girico Preço Venda Compra - MF Rural29 março 2025
Girico Preço Venda Compra - MF Rural29 março 2025 -
![Pokémon Gold & Silver: Earl's speech mannerisms & “winner is you” reference [JPN vs ENG]](https://kantopia.files.wordpress.com/2017/10/earlgymscreenshot.png) Pokémon Gold & Silver: Earl's speech mannerisms & “winner is you” reference [JPN vs ENG]29 março 2025
Pokémon Gold & Silver: Earl's speech mannerisms & “winner is you” reference [JPN vs ENG]29 março 2025 -
 Capitals' Alex Ovechkin Voted Best Shot, Nicklas Backstrom Voted Best Passer By NHL Players29 março 2025
Capitals' Alex Ovechkin Voted Best Shot, Nicklas Backstrom Voted Best Passer By NHL Players29 março 2025 -
 Clowny Piggy Roblox Coloring Page - Free Printable Coloring Pages29 março 2025
Clowny Piggy Roblox Coloring Page - Free Printable Coloring Pages29 março 2025 -
 Como ver a nota do Enem 2022, passo a passo - Guia do Estudante29 março 2025
Como ver a nota do Enem 2022, passo a passo - Guia do Estudante29 março 2025