Malware analysis Malicious activity
Por um escritor misterioso
Last updated 28 março 2025
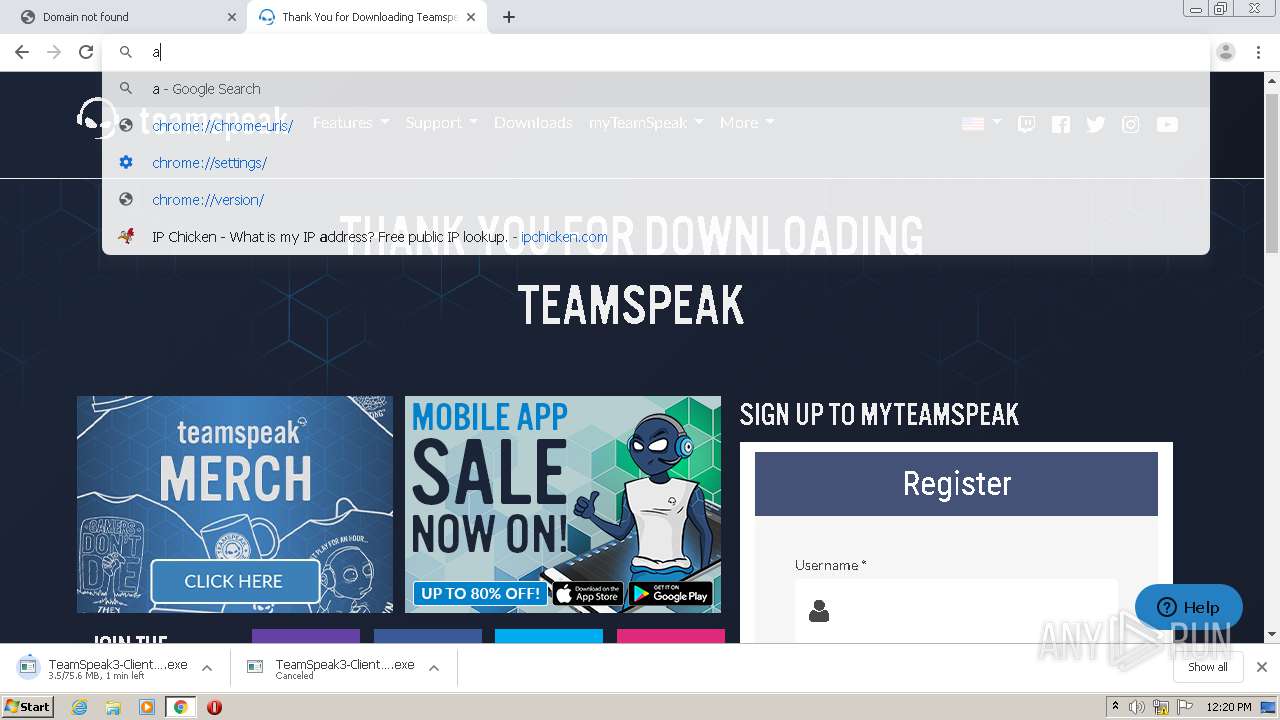

How to Analyze Malware's Network Traffic in A Sandbox

What to Include in a Malware Analysis Report

Advanced Automated Malware Analysis – Kaspersky Research Sandbox

Malware analysis tt.7z Malicious activity

Endpoint Detection and Response, Free - What is EDR Security?

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Remediation and Malware Detection Overview

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity
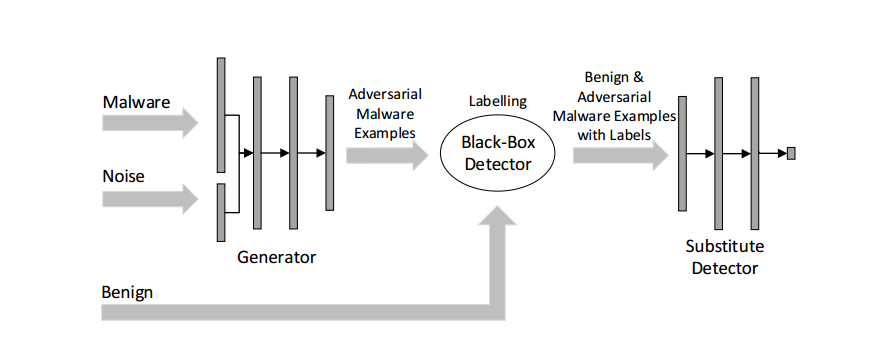
Malware Detection

Malware analysis index.html Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis: Protecting Your Network from Cyber Attacks

Malware analysis metasploit.bat Malicious activity
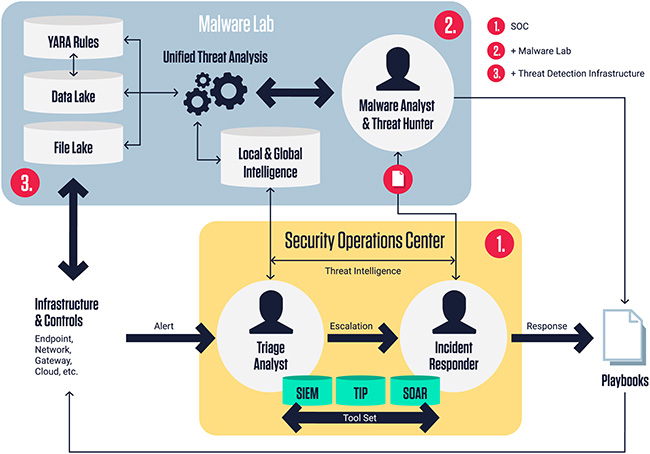
ReversingLabs Malware Lab: Detect, classify, analyze, and respond to malicious files - Help Net Security

Malware Analysis: Steps & Examples - CrowdStrike
Recomendado para você
-
ipchicken.com Traffic Analytics, Ranking Stats & Tech Stack28 março 2025
-
 How to extract your outside IP address - What's My IP - IP Chicken - IP Monkey28 março 2025
How to extract your outside IP address - What's My IP - IP Chicken - IP Monkey28 março 2025 -
ipchicken|TikTok Search28 março 2025
-
SOLVED] Port Forwarding for IP Camera not working28 março 2025
-
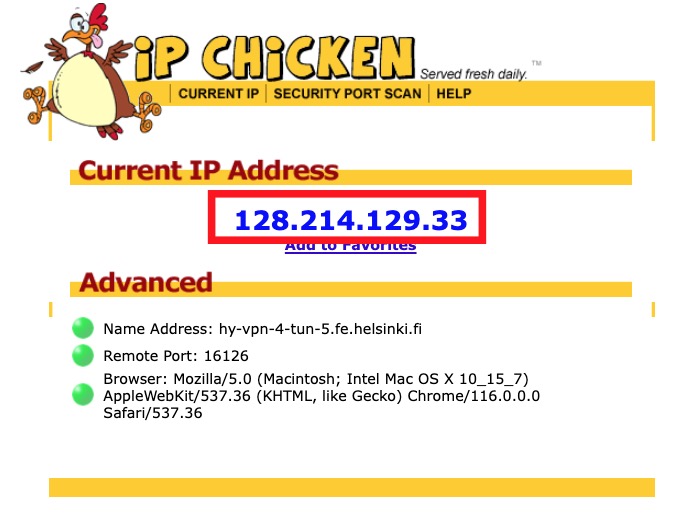 HY-VPN – Checking functionality and errors (Linux)28 março 2025
HY-VPN – Checking functionality and errors (Linux)28 março 2025 -
 28 IP Chicken Recipes28 março 2025
28 IP Chicken Recipes28 março 2025 -
 Finding Your Raspberry Pi's IP Address: A Quick Guide - Linux28 março 2025
Finding Your Raspberry Pi's IP Address: A Quick Guide - Linux28 março 2025 -
 How to Find Your IP Address using IP Chicken Website28 março 2025
How to Find Your IP Address using IP Chicken Website28 março 2025 -
 IP Chicken Quick and Easy Pressure Cooker Chicken - The Spicy Apron28 março 2025
IP Chicken Quick and Easy Pressure Cooker Chicken - The Spicy Apron28 março 2025 -
 IP Chicken and dumplings : r/instantpot28 março 2025
IP Chicken and dumplings : r/instantpot28 março 2025
você pode gostar
-
 Vergil has his own theme for Devil May Cry 5: Special Edition, listen to it here – Destructoid28 março 2025
Vergil has his own theme for Devil May Cry 5: Special Edition, listen to it here – Destructoid28 março 2025 -
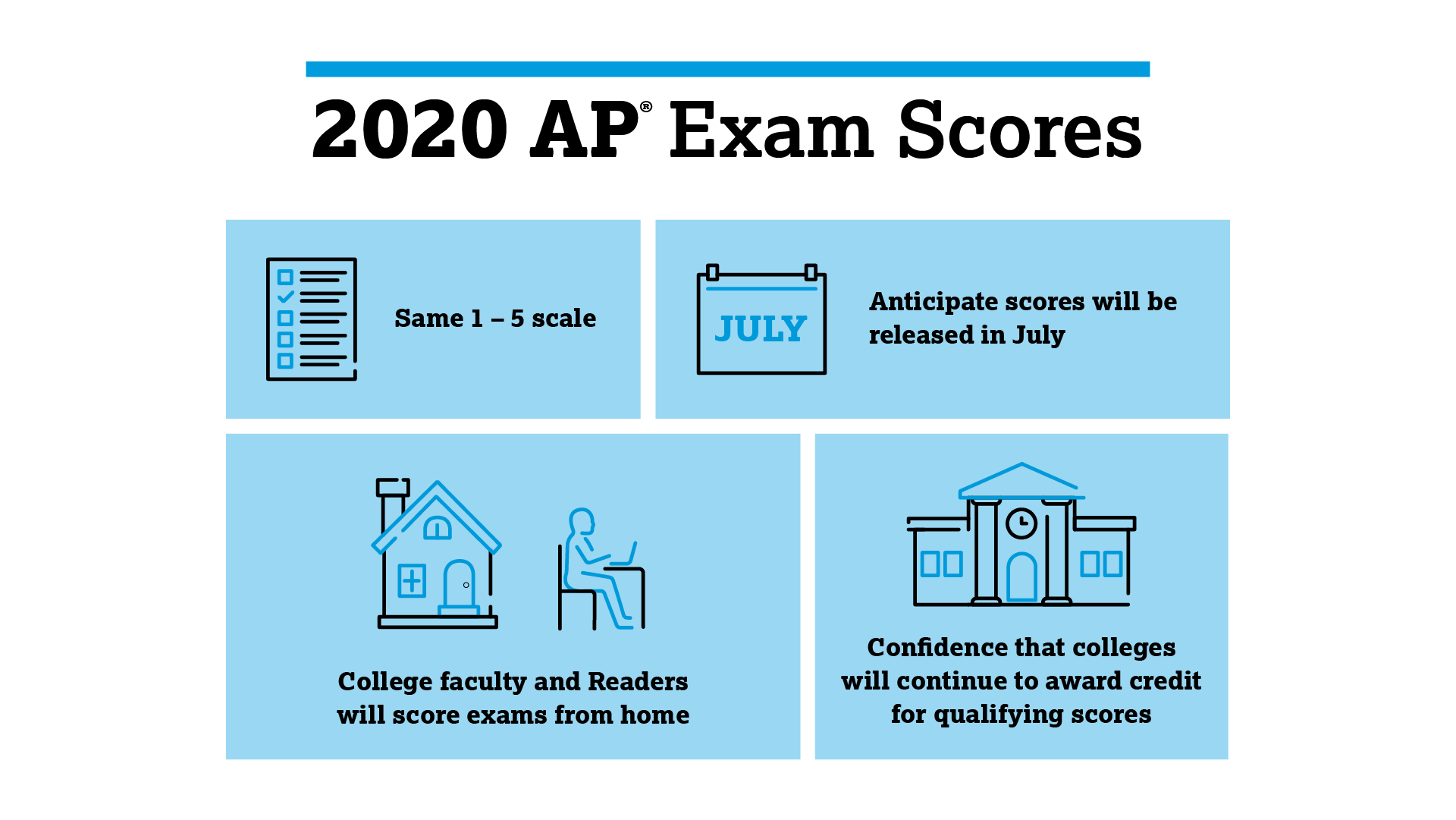 College Board on X: As usual, 2020 AP Exams will be scored by our28 março 2025
College Board on X: As usual, 2020 AP Exams will be scored by our28 março 2025 -
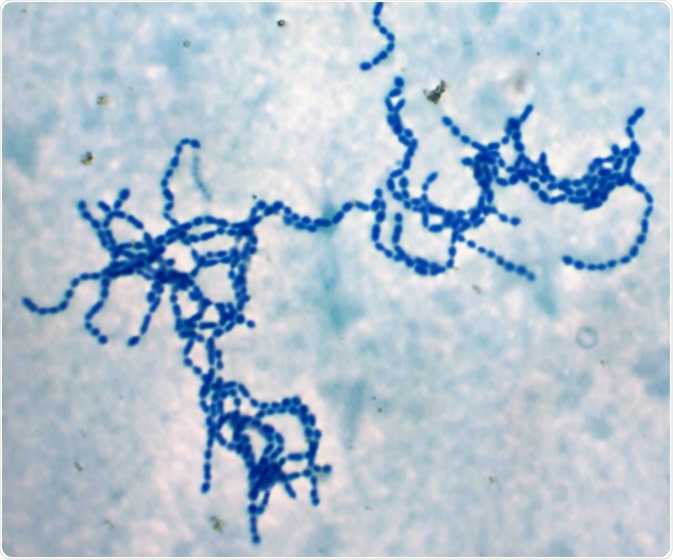 What is Toxic Shock Syndrome?28 março 2025
What is Toxic Shock Syndrome?28 março 2025 -
 Goku UI Transform28 março 2025
Goku UI Transform28 março 2025 -
 Chelsea FC REACH AGREEMENT in PRINCIPLE to FINISH SIGNING!✓Kendry Paez Chelsea TRANSFER DONE DEAL!🤩28 março 2025
Chelsea FC REACH AGREEMENT in PRINCIPLE to FINISH SIGNING!✓Kendry Paez Chelsea TRANSFER DONE DEAL!🤩28 março 2025 -
 Boruto: Naruto Next Generations - Qual a história e onde assistir ao anime?28 março 2025
Boruto: Naruto Next Generations - Qual a história e onde assistir ao anime?28 março 2025 -
SUPER SABADO EN AJEDREZ MARTELLI - Ajedrez Martelli28 março 2025
-
 Watch Saw: The Final Chapter28 março 2025
Watch Saw: The Final Chapter28 março 2025 -
 Mortal Kombat 4 Arcade Marquee - 26 x 8 - Arcade Marquee Dot Com28 março 2025
Mortal Kombat 4 Arcade Marquee - 26 x 8 - Arcade Marquee Dot Com28 março 2025 -
 Minha Vez - Ton Carfi (Clipe Oficial)28 março 2025
Minha Vez - Ton Carfi (Clipe Oficial)28 março 2025

