Detecting Linux Anti-Forensics: Timestomping
Por um escritor misterioso
Last updated 28 março 2025
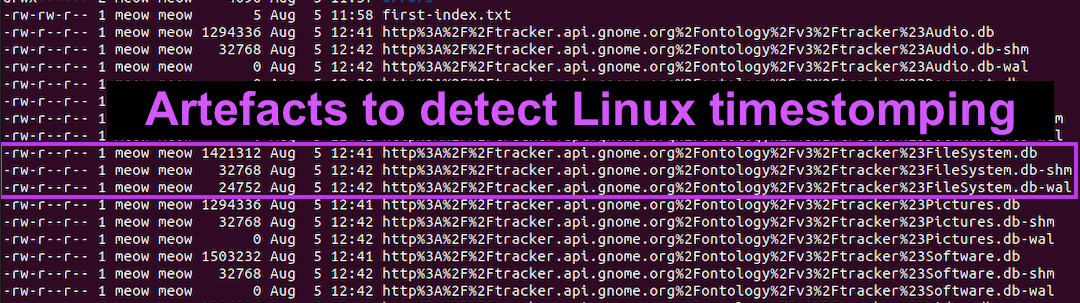
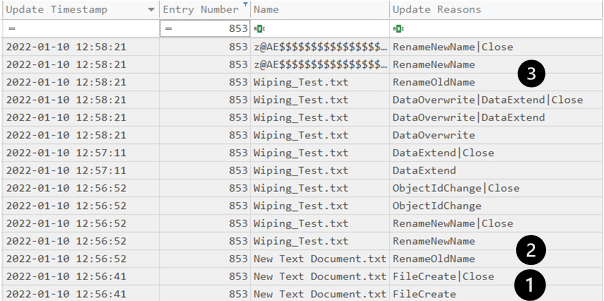
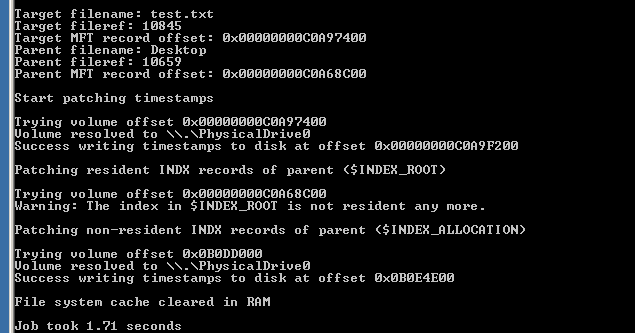
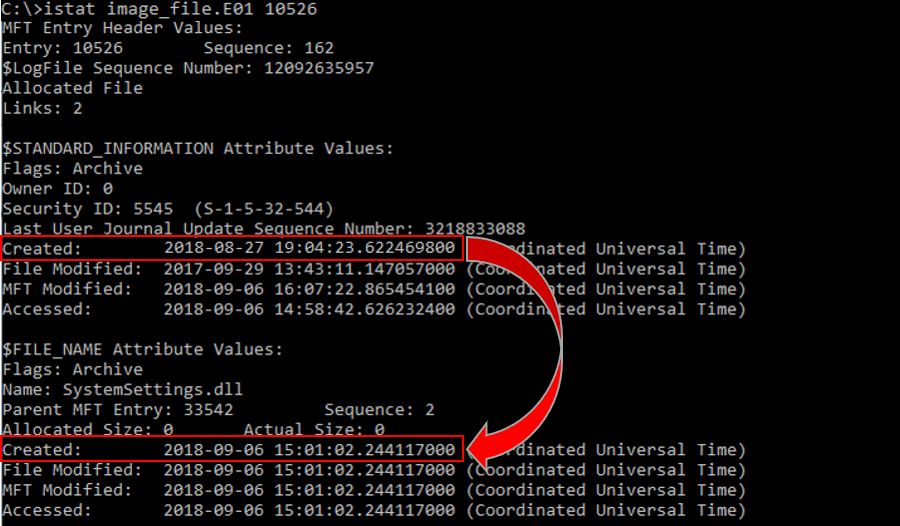
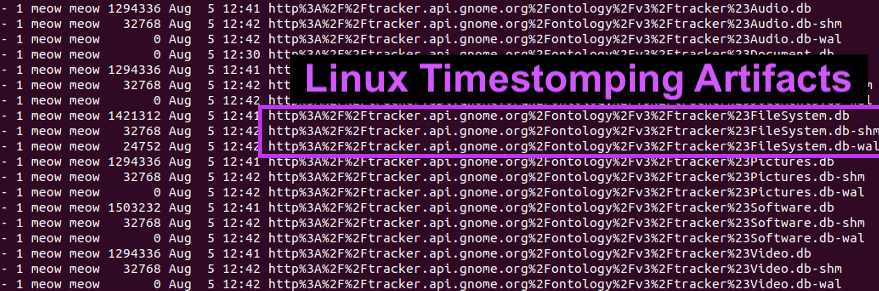
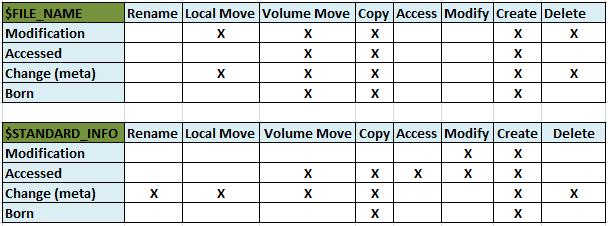
#160; Threat actors can modify the timestamps on malicious files to evade detection. This technique has been used time and time again across va

A survey on anti-forensics techniques
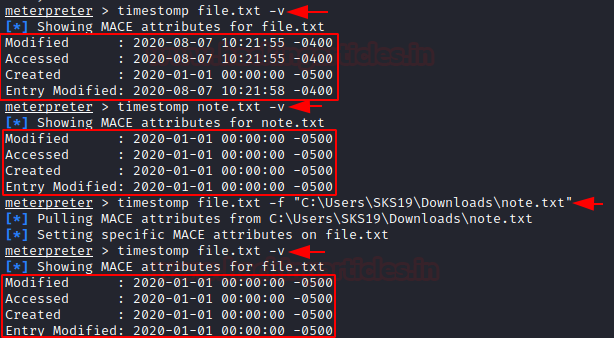
Anti-Forensic: Swipe Footprint with Timestomp - Hacking Articles

PDF) Artifacts for Detecting Timestamp Manipulation in NTFS on
Anti-Forensics Techniques - Cynet
inversecosᵘʷᵘ's Threads – Thread Reader App
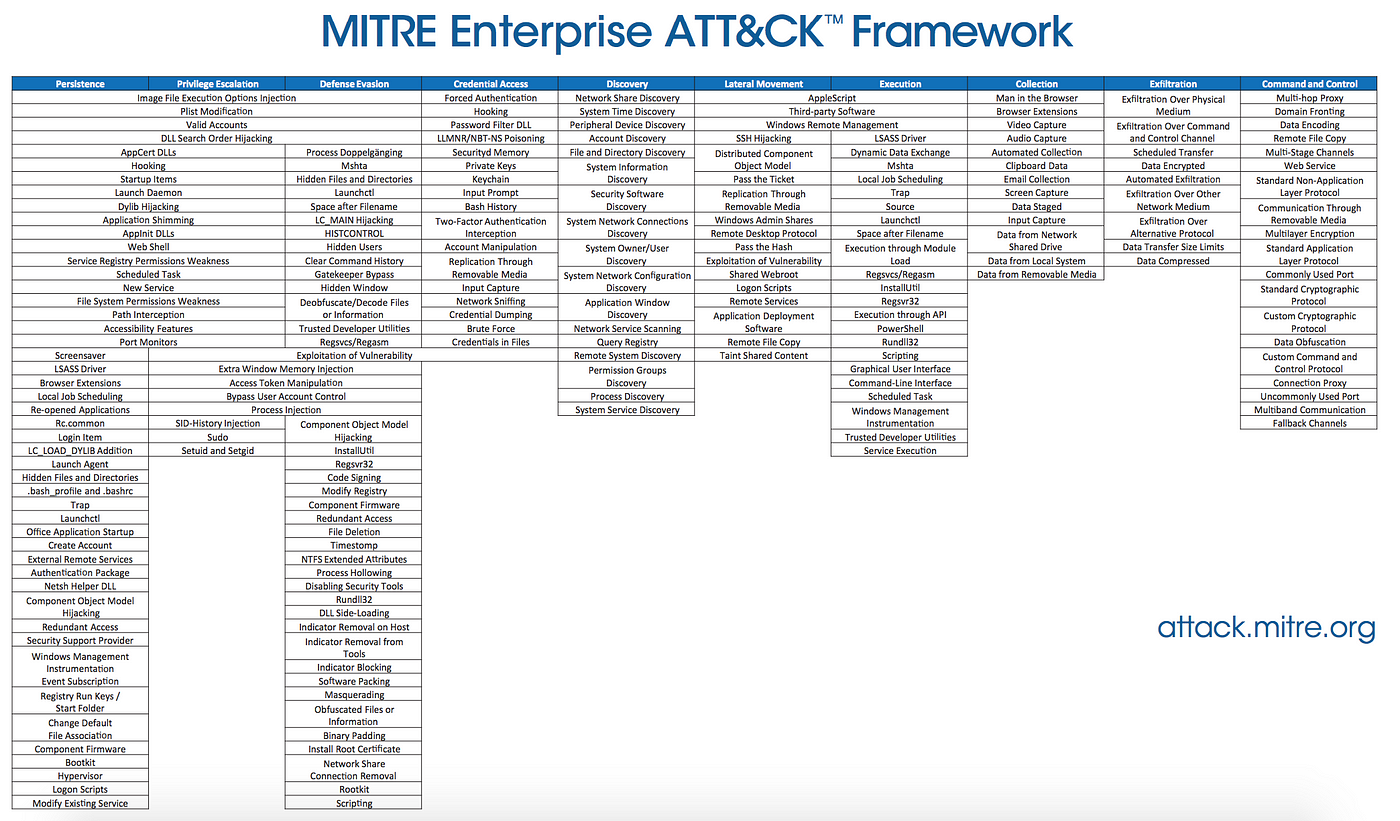
Forensic detection of MITRE ATT&CK Techniques

Detecting Linux Anti-Forensics: Timestomping
Anti-Forensics Techniques - Cynet
SANS Digital Forensics and Incident Response Blog
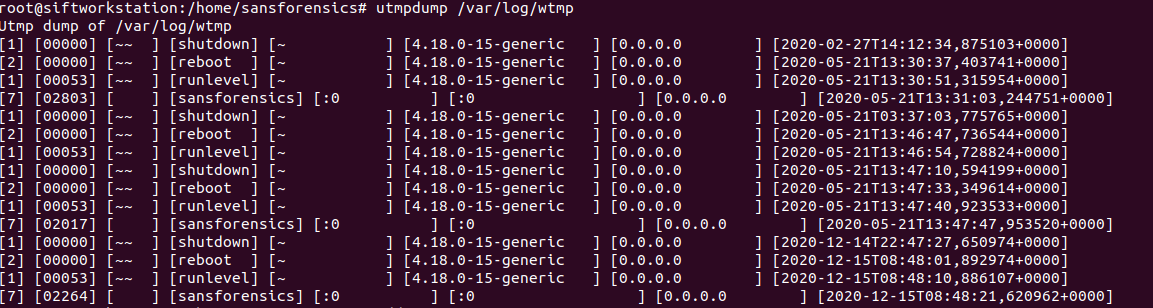
Detecting Linux Anti-Forensics Log Tampering

5 anti-forensics techniques to trick investigators (+ examples
Recomendado para você
-
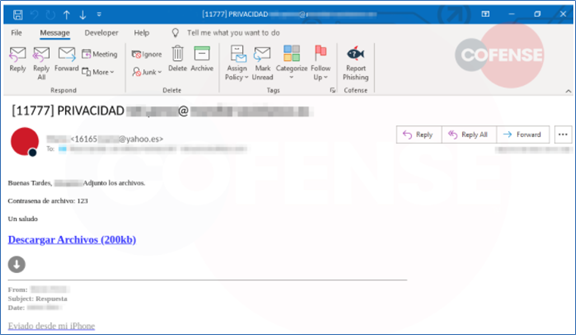
 Reference attack model: an attacker embeds a malicious script into28 março 2025
Reference attack model: an attacker embeds a malicious script into28 março 2025 -
 Evade - Script, Fluxus28 março 2025
Evade - Script, Fluxus28 março 2025 -
 Tbao Hub Evade Mobile Script28 março 2025
Tbao Hub Evade Mobile Script28 março 2025 -
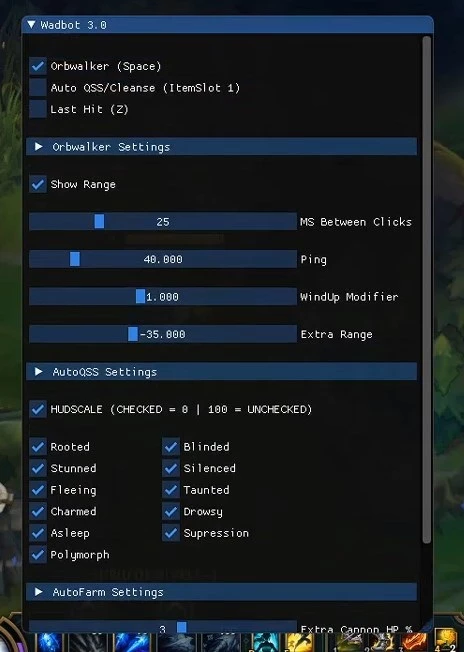 Script Legit Auto Farm, Evade, Combo - League Of Legends Lol - DFG28 março 2025
Script Legit Auto Farm, Evade, Combo - League Of Legends Lol - DFG28 março 2025 -
 Tumors exploit FTO-mediated regulation of glycolytic metabolism to evade immune surveillance - ScienceDirect28 março 2025
Tumors exploit FTO-mediated regulation of glycolytic metabolism to evade immune surveillance - ScienceDirect28 março 2025 -
 XWorm, Remcos RAT Evade EDRs to Infect Critical Infrastructure28 março 2025
XWorm, Remcos RAT Evade EDRs to Infect Critical Infrastructure28 março 2025 -
 how to be a mob in evade|TikTok Search28 março 2025
how to be a mob in evade|TikTok Search28 março 2025 -
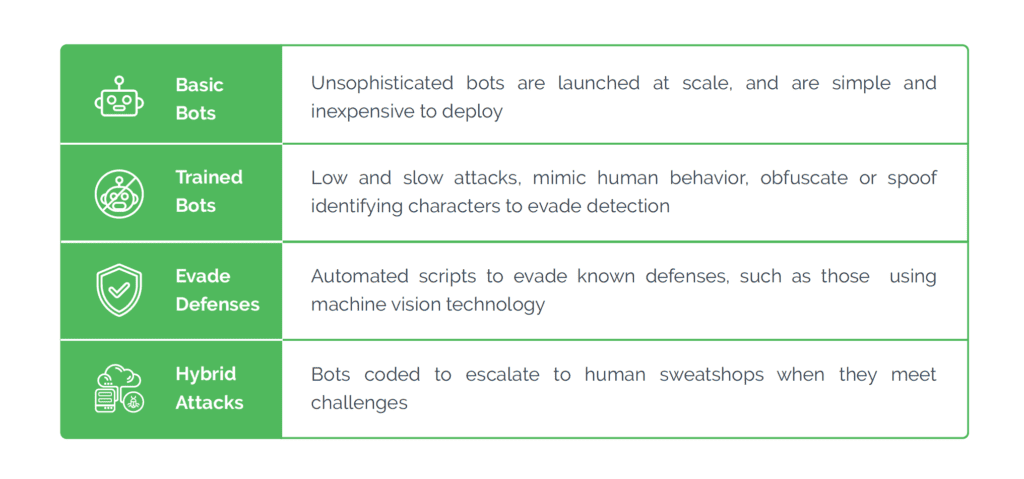 What Is Bot Detection?28 março 2025
What Is Bot Detection?28 março 2025 -
 How Oklahoma State mounted a double-digit comeback to evade Houston and remain in the Big 12 title race28 março 2025
How Oklahoma State mounted a double-digit comeback to evade Houston and remain in the Big 12 title race28 março 2025 -
 Metamorfo Banking Trojan Leverages AHK compiler to Evade Detection28 março 2025
Metamorfo Banking Trojan Leverages AHK compiler to Evade Detection28 março 2025
você pode gostar
-
 Jogo Pes 21 futebol Efootball Pro Evolution Soccer 2021 Ps4 em28 março 2025
Jogo Pes 21 futebol Efootball Pro Evolution Soccer 2021 Ps4 em28 março 2025 -
 Learn to Fly 3 Unblocked28 março 2025
Learn to Fly 3 Unblocked28 março 2025 -
 Refugee” Alan Gratz Vocabulary Crossword list 2 Crossword28 março 2025
Refugee” Alan Gratz Vocabulary Crossword list 2 Crossword28 março 2025 -
 Dragon Ball Z Novo filme terá Freeza e Bills - veja o cartaz28 março 2025
Dragon Ball Z Novo filme terá Freeza e Bills - veja o cartaz28 março 2025 -
 Desenho de Emoji ninja para colorir Desenhos para colorir e imprimir gratis28 março 2025
Desenho de Emoji ninja para colorir Desenhos para colorir e imprimir gratis28 março 2025 -
 KIT DES CR REXONA CLINICAL CLASSIC C/3 48G - alexfarma28 março 2025
KIT DES CR REXONA CLINICAL CLASSIC C/3 48G - alexfarma28 março 2025 -
 Darkseid - Wikipedia28 março 2025
Darkseid - Wikipedia28 março 2025 -
 Os flintstones o filme dvd original lacrado dublado em Promoção na Americanas28 março 2025
Os flintstones o filme dvd original lacrado dublado em Promoção na Americanas28 março 2025 -
 TODAS AS ILHAS DE BLOX FRUIT ATÉ O LEVEL 300 ! ( Blox Fruit28 março 2025
TODAS AS ILHAS DE BLOX FRUIT ATÉ O LEVEL 300 ! ( Blox Fruit28 março 2025 -
 Minecraft : Giant Steve Papercraft28 março 2025
Minecraft : Giant Steve Papercraft28 março 2025